From Data to Defense: How to Better Integrate IT with OT
The idea of technological convergence is not exactly new. By integrating different technologies and making them work together efficiently as a single, cohesive system, companies can increase their efficiency, reduce errors, lower costs, improve workflows and achieve measurable competitive advantages.
Enterprise IT has long been at the center of convergence efforts, which aim to bring together the, often disparate, technologies in data centers and support seamless interoperability. One example of convergence is the emergence of converged IT infrastructure, which later evolved into hyperconverged infrastructure. These developments combine traditionally separate servers, storage, networks and management tools into a single, cohesive product that is deployed once and managed centrally.
IT/OT convergence aims to integrate physical operational technology (OT) assets and devices into the digital information technology (IT) landscape. Advances in machine-to-machine communication and the development of sophisticated IoT sensors and actuators enable this integration. These devices, attached to physical equipment, use standardized network protocols like TCP/IP to transmit data from each system to different central servers for operations, monitoring and analysis. The insights gained from this analysis are then relayed back to the physical systems, enhancing (autonomous) operations, improving accuracy, facilitating maintenance, and increasing uptime.
The Impact of IT/OT Convergence
Consider how IT/OT convergence impacts everyday technologies, such as trains. By integrating sensors, actuators, and standardized communication protocols, vehicles can transmit real-time data on their position, motion, and condition to a centralized collection point for analysis. Simultaneously, these vehicles can receive real-time information, like traffic updates, weather conditions or important public information. This helps both passengers and drivers make better decisions, such as choosing alternative routes around the city or performing early maintenance to prevent breakdowns. This convergence of IT and OT is similarly fundamental to the development of autonomous vehicles, or self-driving cars.
Types of IT/OT Convergence
IT/OT convergence isn’t a single initiative; it can vary based on the needs and goals of an organization. The three main types of IT/OT convergence are:
- Process Convergence: This involves the integration of workflows. IT and OT departments align their processes to support each other, ensuring clear communication on critical projects. This organizational convergence focuses on internal business structures. For instance, data storage and protection processes in IT might need adjustments to accommodate OT systems.
- Software and Data Convergence: This focuses on designing front-office software and data to meet OT needs, involving changes in network architecture. IT departments might implement new tools to collect and analyze data from both OT and IT systems, enhancing business analytics and decision-making.
- Physical Convergence: This involves updating or retrofitting physical devices with new hardware to integrate IT with traditional OT. This operational convergence ensures that hardware is continuously updated and maintained, potentially involving new OT systems or retrofit devices for data communication and control.
In practice, industries increasingly integrate sensors and networked systems, such as wireless Sensor and Actuator Networks (WSANs: interconnected networks of sensors and actuators that communicate wirelessly), to manage environments like water treatment plants, power grids, and factories. This integration, part of the IoT and often referenced as Industry 4.0, combines automation, communication, and networking in industrial settings. The addition of OT to IT allows organizations to leverage data generated by OT through IoT devices and edge computing more effectively.

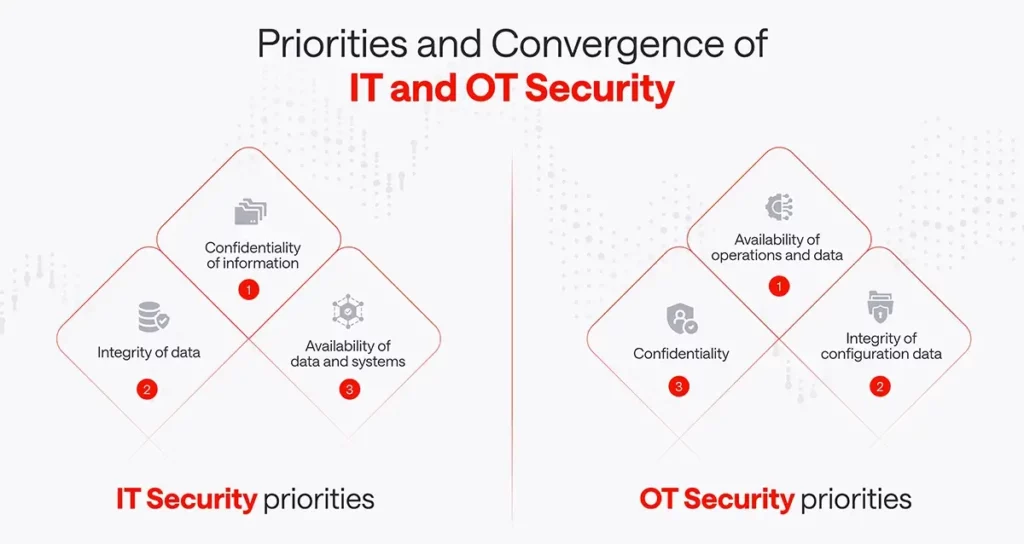
The Downer: Security Challenges in IT/OT Convergence
IT/OT convergence introduces significant IoT security challenges. This integration merges not just technologies but also teams and processes. Cybersecurity teams must adapt to the unique real-time and availability related requirements of industrial environments. For example, it’s impossible to shut down a smart grid for several hours to apply patches, reboot and test different configurations. OT systems, which typically remain operational for decades with planned hardware replacement intervals, bring different kinds of security risks. Systems not originally designed for internet connectivity need retrofitting with IoT devices and appropriately designed security measures to ensure appropriate protection.
Your 7 Key Security Considerations for IT/OT Convergence
1. Lack of Collaboration
IT and OT teams often use different professional language, which needs to be made transparent, so they don’t work in their own silos, creating security gaps, increase complexity, and have redundant efforts. Ensuring security in a converged environment requires these teams to prioritize collaboration and communication, which has previously not always been the norm.
2. Increased Attack Surface
Integrating IT and OT increases the attack surface for cyber threats. Connecting IT and OT networks makes existing vulnerabilities exposed. There are different attack vectors, which need to beharmonized against the different security requirements of IT and OT management.
3. Security Gaps and Vulnerabilities
The convergence exposes previously undetected security gaps and vulnerabilities, with different security practices: OT systems, traditionally isolated, have less stringent security protocols than IT systems taking exposure more into account. As OT systems for different sectors have to be certified according to different standards, these certification take up a certain amount of time in the organization. Therefore, immediate patching is more of an exception than the norm. As this is more of a regulatory issue than a security requirement, the vulnerabilities remain unpatched, nonetheless.
4. Legacy OT Systems
While IT systems typically have a lifespan of less than five years, OT systems, such as production machines, can operate for decades with the same engineered firmware. These legacy systems often lack security features and cannot be upgraded due to the aforementioned regulatory requirements or operational contracts. Every converged system needs a thorough security audit, and outdated OT equipment that cannot meet security requirements may need to be isolated or updated or if this not possible, replaced.
5. Inadequate Visibility
IT relies on asset discovery and configuration for a complete picture of the managed environment. OT systems must provide similar visibility, enabling discoverability, remote configuration, and management. Without visibility into OT devices, administrators cannot secure or manage them, leading to potential security breaches.
6. Availability Requirements
OT production systems need to be operated 24/7, all year round, and cannot be paused for upgrades or updates without significant revenue loss or physical risk. For instance, shutting down life-support medical equipment for software updates is not an option. And given the amount of spare medical equipment in hospitals, this comes as an even bigger challenge. Organizations might therefore argue against patching security vulnerabilities due to the inability to afford the necessary downtime for fixes.
7. Impact of Disruptions
While integration generally brings benefits, disruptions can be devastating. For example, a network disruption, such as a failure of network equipment or an external DoS attack, can halt communication on a factory floor with active machines. IT/OT convergence requires a careful assessment of resilience and fail-safe measures to mitigate such risks.
What You Need to Succeed: Holistic Approach to Security
A converged IT/OT environment requires a holistic cybersecurity approach with a consistent security policy: uniform security policies and protocols for both environments help close security gaps and improve overall security. A holistic security approach can improve resilience against cyber-attack, a faster threat detection and quick response channels minimize the impact of cyberattacks on operations. As many regulations demand a comprehensive security strategy encompassing both IT and OT, a well-done convergence aids in meeting compliance regulations and regulatory requirements and the integrated security architecture simplifies the demonstration and documentation of security measures to regulatory authorities.
As the convergence can allow for centralized monitoring and control of security measures, enabling quicker threat identification and response, your cybersecurity tools should leverage this too. A well-done integration can also enhance the efficiency and speed of implementing security measures with:
- Real-time data and analytics: Using real-time data from both environments enables faster threat detection and analysis.
- Automation of security solutions: Convergence facilitates the use of automated security solutions that can detect and react to threats in real-time.
IT/OT Convergence and Cybersecurity: Better Go Agentless!
Agentless cybersecurity solutions are particularly suitable for OT environments because they offer several advantages:
- First, they minimize operational disruptions because OT systems must run continuously and must not be interrupted for the installation or maintenance of agents.
- Second, they support older systems that are often not compatible with modern software agents.
- Third, an endpoint agent often needs to have internet connectivity, which is especially in critical environments seldom the case.
- Fourth, they are easier and faster to implement and maintain because no endpoint installation is required.
- Fifth, there is no impact on CPU and memory usage for real-time operational requirements.
- Sixth, they provide a more comprehensive network view because they collect data directly from network devices and interfaces.
- Finally, they enable compliance with strict security and compliance regulations because they can be deployed behind a data diode therefore providing absence of interference for certified environments.
Conclusion and To-Do’s:
The convergence of IT and OT is critical to cybersecurity because it enables a more comprehensive security strategy that covers both information and operational technologies. This integration helps to reduce the attack surface, close security gaps, improve efficiency and responsiveness, ensure business continuity, and meet compliance requirements.
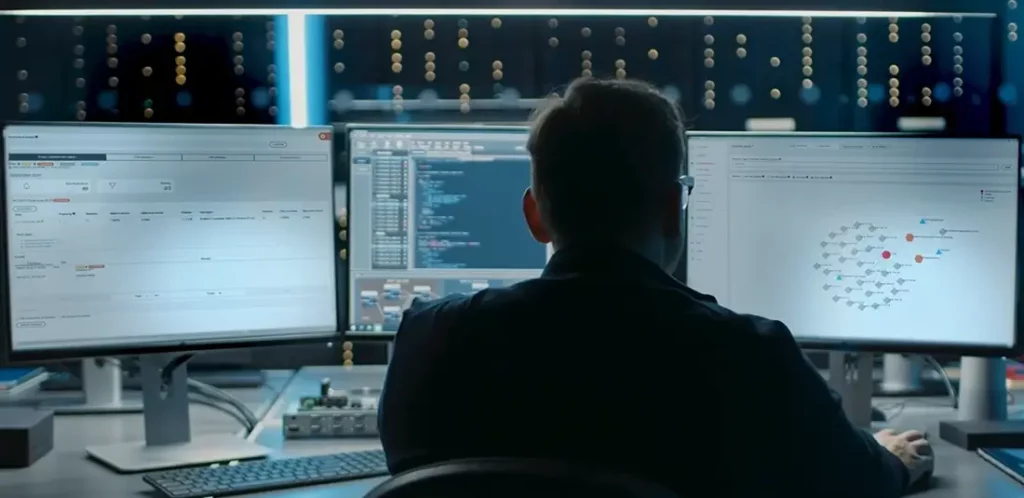
Next-generation Network Detection & Response (NDR) solutions like ExeonTrace provide comprehensive cybersecurity for enterprises. It builds a unified view from network metadata, allowing continuous analysis and monitoring of IT-, cloud-, and OT-networks via a single application. This prevents attackers from moving undetected between these environments, exploiting vulnerabilities, infiltrating infrastructure, or bypassing security measures.
The solution employs powerful AI algorithms to automatically detect suspicious behavior. It analyzes network data flows, identifies potential cyber threats efficiently and effectively. This approach is unlike traditional NDR solutions that solely rely on traffic mirroring (which can be expensive or impractical due to encryption and high bandwidths) and uses lightweight traffic metadata. It doesn’t require expensive data mirroring or packet decryption for analysis. Its algorithms work for both encrypted and unencrypted traffic.
Solutions analyzing payload become blind due to widespread encryption, while Exeon remains effective. Should you be hard pressed to do so, our solution can interact perfectly well with deep packet inspection solutions for critical points where you need to have protocol visibility in your environment.