Modern Attackers Don’t Break In – They Log In

Why the WEF Cybersecurity Outlook 2026 makes a strong case for UEBA In the past, cybersecurity was largely about keeping attackers out. Today, that paradigm no longer holds. According to the World Economic Forum’s Global Cybersecurity Outlook 2026, published this week during the WEF Annual Meeting in collaboration with Accenture, the most damaging cyber incidents are increasingly driven by legitimate identities, valid credentials and trusted access paths – not by broken perimeters or exotic exploits. This shift has profound implications for how organizations detect, investigate and contain threats. Why it matters: what’s changing in the threat landscape The 2026 Outlook highlights several trends that, taken together, point to a fundamental detection gap. 1. Identity-driven attacks are accelerating These attacks rarely look “malicious” at first glance. They are executed using: Traditional security controls were not designed to detect these identity-driven attacks. 2. AI is amplifying attackers and defenders AI is no longer just a defensive capability. The report shows that: This dramatically increases the volume, speed and subtlety of suspicious behavior. Detection approaches that rely on static rules or manual correlation alone simply cannot keep up. 3. Resilient organizations invest in analytics, not just controls One of the most telling findings of the Outlook is the difference between highly resilient and insufficiently resilient organizations. More resilient organizations: In contrast, less resilient organizations struggle with alert fatigue, fragmented visibility and slow response times – even when they have SIEMs and SOCs in place. Why traditional detection struggles Most security stacks are still optimized for: But identity-driven attacks don’t trip those wires. Common failure modes include: The result: organizations detect breaches late – if at all. Why behavior analytics (UEBA) closes the gap User and Entity Behavior Analytics (UEBA) addresses the challenges highlighted in the WEF report. Instead of asking “Is this known to be malicious?”, UEBA asks: […]
New UEBA solution by Exeon Analytics complements Exeon.NDR
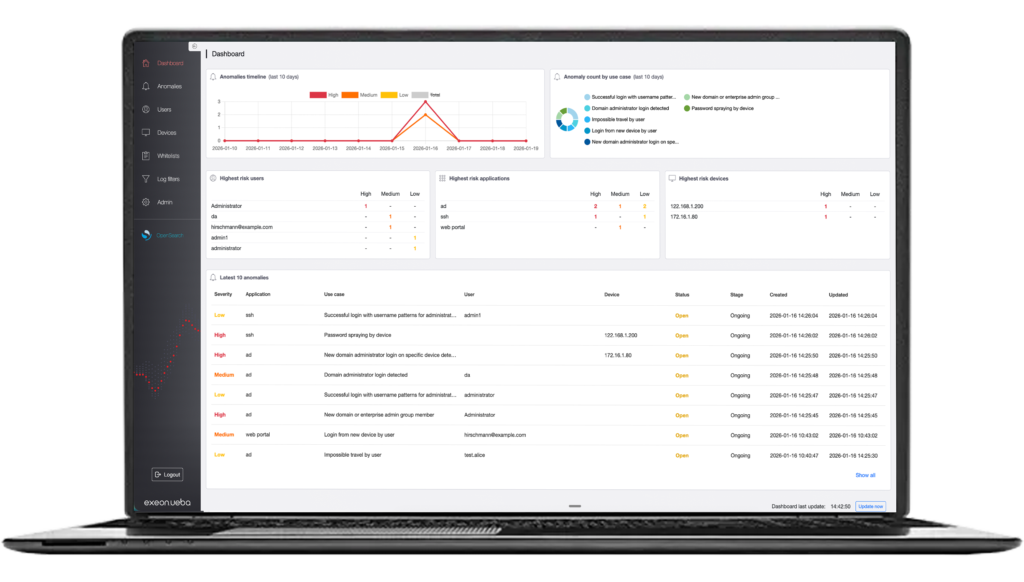
Modern cyberattacks are no longer carried out by exploiting technical vulnerabilities. Instead, attackers rely on compromised credentials, legitimate privileges, or internal accounts. As a result, attacks increasingly originate from within and often remain undetected for long periods by traditional security solutions. Exeon Analytics, the Swiss cybersecurity specialist, announces today Exeon.UEBA, the new solution for analyzing user, entity, and application behavior that directly addresses this type of […]
IoT Security: Closing the Detection Gap

Facing rising cyber risks, industrial infrastructure needs unified defenses: metadata visibility, behavioral detection, and SOC integration—for true resilience.
Phishing Despite Active MFA

MFA is no longer enough. Attackers use phishing to steal credentials and move laterally—completely undetected. Tools like EDR, XDR & SIEM often miss these threats. Real-time Network Detection & Response and User Entity Behavior Analytics spot suspicious activity before attackers gain control.
