Highly scalable, privacy-compliant User and Entity Behavior Analytics (UEBA) for SAP
Modern attackers don’t break into SAP – they log in.
Exeon.UEBA detects suspicious behavior across SAP identities, transactions, tables, and clients – in real time and with full data sovereignty.
Why UEBA Matters Today for SAP
Credential Abuse
Credential abuse remains a leading breach pattern in 2025.
(Verizon DBIR 2025)
AI-Driven Social Engineering
72% of organizations report rising cyber risk driven by AI-enabled attacks.
(SoSafe Cybercrime Trends 2025)
Ransomware impact on ERP
78% of organizations experienced ransomware in the past year.
(CrowdStrike State of Ransomware 2025)
Supply chain exposure
Third-party involvement continues to grow as a major breach factor.
(Verizon DBIR 2025)
Why Exeon.UEBA for SAP
Easy-to-integrate behavior analytics for identities, applications & data
Unified SAP identity and application visibility
Monitor SAP users, admins, service accounts, and interfaces across on-prem and cloud in one behavioral view.
Flexible log onboarding for SAP landscapes
Quick onboarding of SAP Security Audit Logs (SAL) and surrounding system logs via standardized log modeling.
Efficient processing for reduced volume & cost
Smart normalization and compression lower SAP log volume while improving detection quality.
Real-time processing for instant SAP threat detection
Stream-based analytics detect suspicious SAP behavior instantly – even at scale.
Dual detection: SAP expert use cases + predictive AI
Prebuilt SAP detections combined with behavioral learning uncover subtle misuse and insider threats.
Privacy-first, sovereign deployment
On-prem or air-gapped operation with encryption and pseudonymization for GDPR-compliant SAP monitoring.
The all-in-one behavioral analytics platform for identities, applications & data
Why Exeon.UEBA
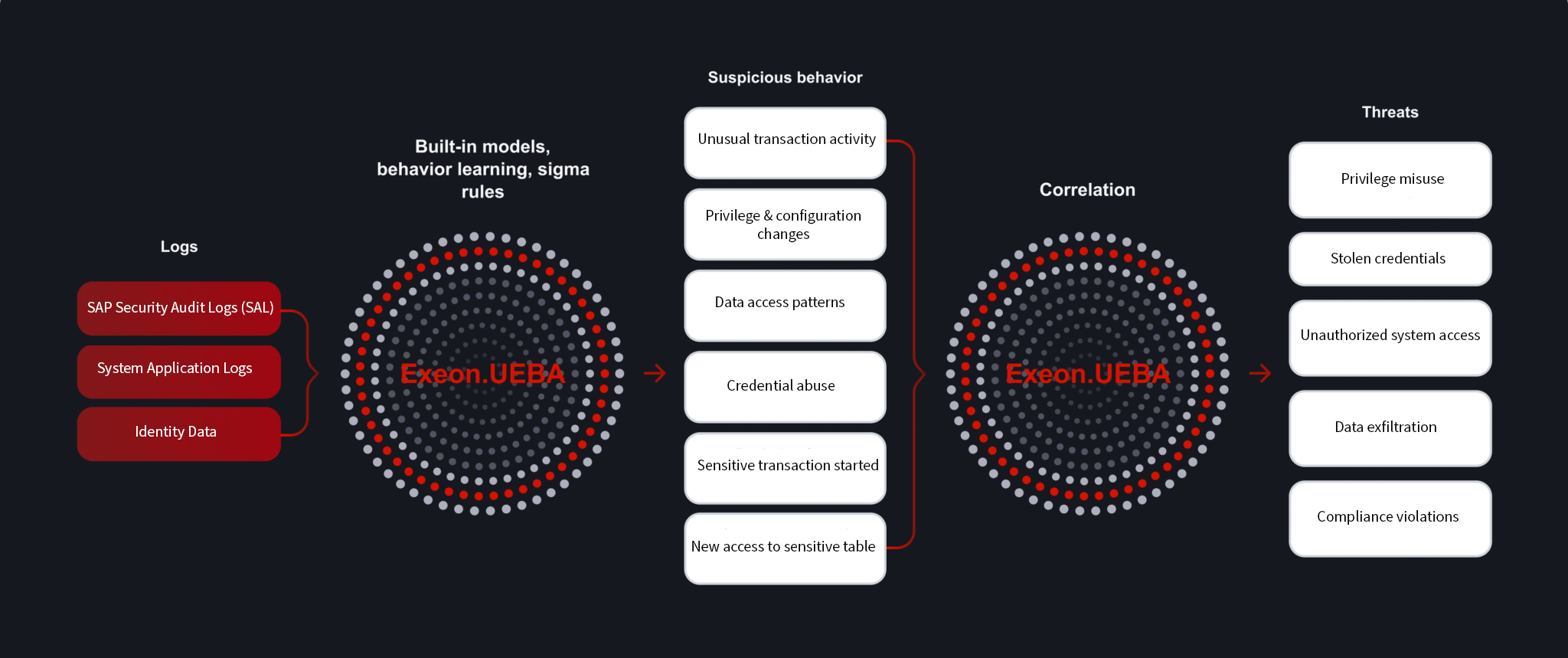
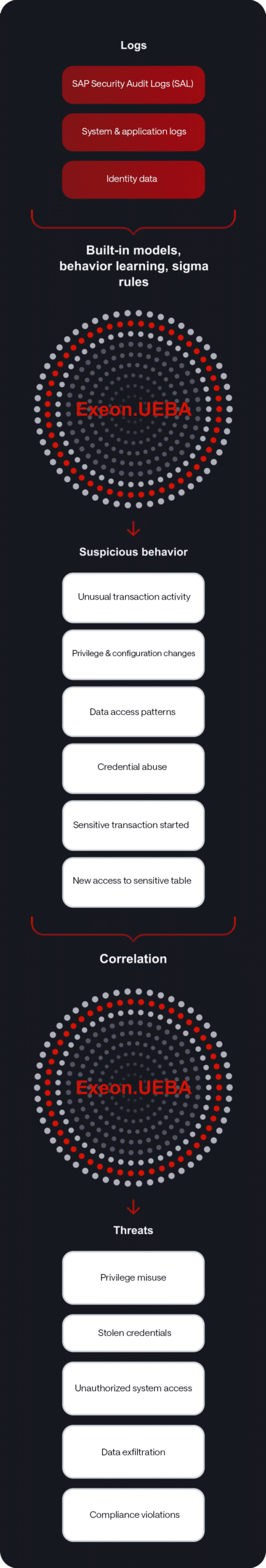
How Exeon.UEBA for SAP Works
Built differently – leveraging Exeon’s proven NDR expertise
Comprehensive log collection
Ingest identity, application and system logs from SaaS/IaaS/IAM provider, infrastructure systems and custom-built applications.
Smart data handling
Deduplication, compression and normalization reduce data volumes, improve detection efficiency and lower SIEM/storage costs.
Flexible detection
Combine expert-built behavioral analyzers with custom rules and AI-driven models for unique environments and specialized use cases.
Real-time alerting and automated response
Stream processing delivers sub-second alerts and allows automated containment actions via SOAR, IAM or ticketing integrations.
Investigation and behavioral timelines
Unified visibility into user and entity behavior across all systems simplifies investigation and improves analyst efficiency.
How Exeon.UEBA for SAP Compares
Approach
No UEBA
UEBA via SIEM
Typical UEBA Tools
Exeon.UEBA for SAP
Visibility
Minimal SAP user and application behavior visibility
Partial visibility; costly, massive SAP log ingestion at scale
Fits standard IT; gaps in proprietary SAP tables and SAL logs
Unified SAP visibility: identities, transactions, and tables
Detection
Misses SAP credential misuse and insider activity
Rule-based/batch-processed: misses subtle SAP behavioral shifts
Mixed under high load; requires manual SAP tuning
Real-time AI detection of SAP misuse (e.g., SAL anomalies)
Operational Impact
High risk: delayed SAP breach detection and zero visibility
Very high SAP log volume and SIE costs; alert fatigue
Moderate complexity and limited flexibility for SAP landscapes
Lower SIEM costs: smart normalization & automated SAP response
Exeon.UEBA for SAP applied to real-world needs
Unusual Activity
Stolen credentials are used in legitimate SAP transactions.
Exeon.UEBA monitors access, actions, and permission changes while learning behavior per user and across environment.
- Identifies critical transactions, unusual behavior of users and admins
- Detects credential misuse early
Privilege Changes
Privilege escalation and critical changes often go unnoticed.
Exeon.UEBA monitors user, role, and password changes while tracking critical transactions and debugger use.
- Detects suspicious configuration manipulation like high-privileged changes
- Prevents attackers from persisting in SAP
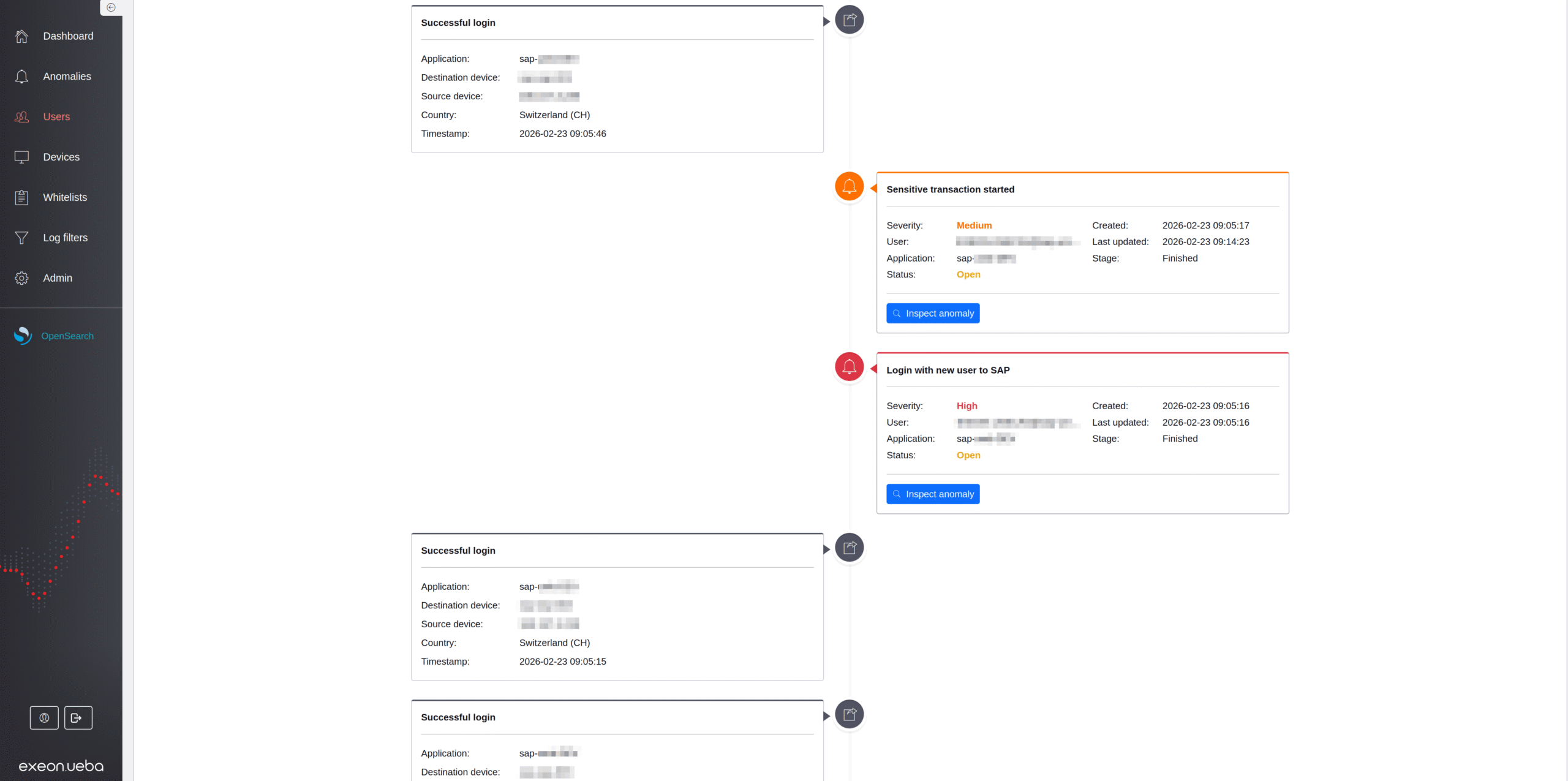
Sensitive Data Access
Data exfiltration via legitimate SAP access blends into normal activity. Exeon.UEBA monitors sensitive tables and direct table access while correlating data export with user behavior.
- Detects abnormal access patterns in HR, finance, or harsh table access
- Reduces the risk of large SAP data breaches
Secure Compliant Monitoring
Regulated industries require SAP monitoring without violating GDPR. Exeon.UEBA offers flexible on-prem or air-gapped deployment and built-in pseudonymization and encryption.
- Ensuring privacy-compliant SAP monitoring
- Enables sovereign SAP security and no disclosure of identity data in external clouds
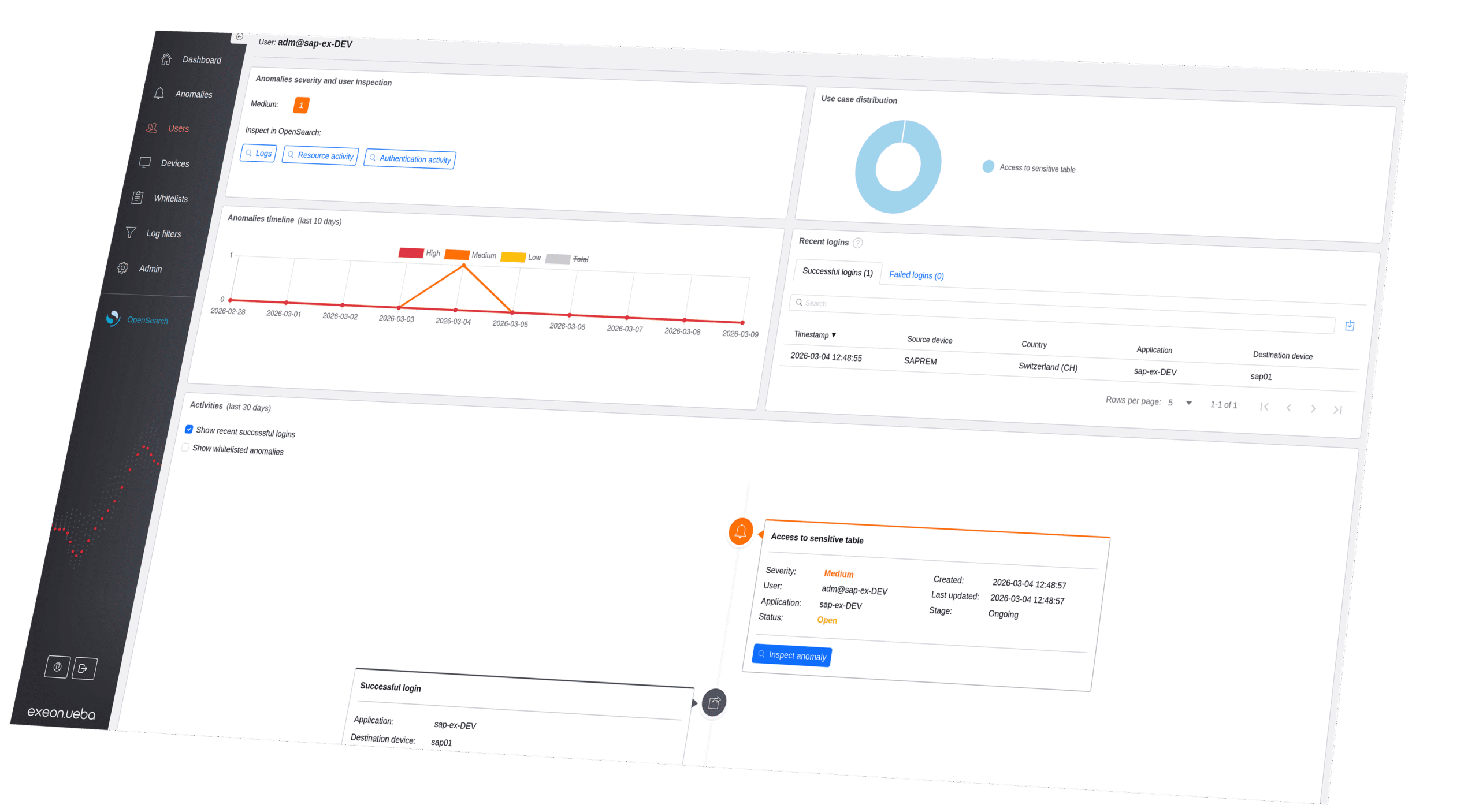
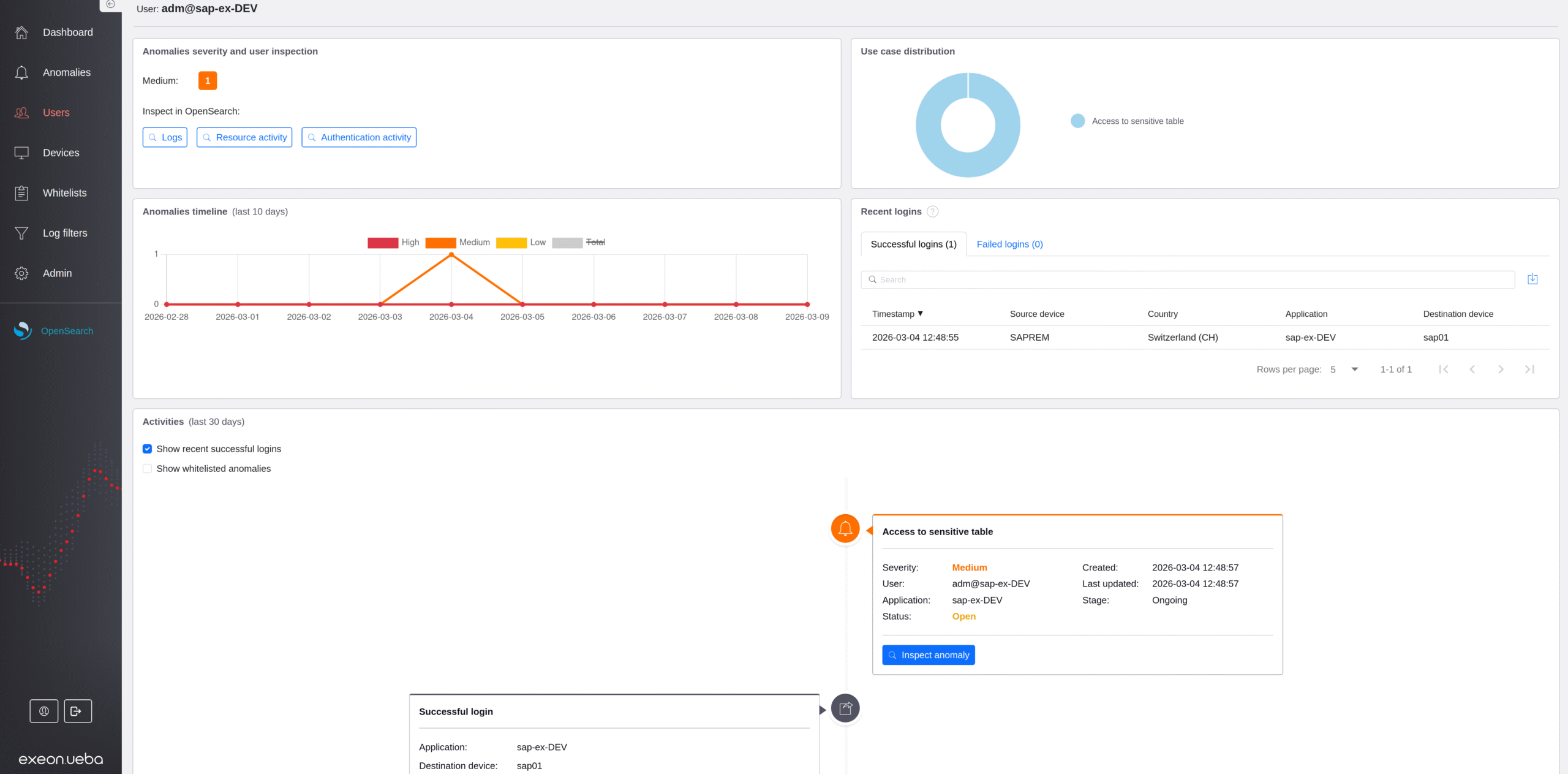
Exeon.UEBA in action
Modern attacks hide within normal identity and application activity.
Exeon.UEBA uncovers these threats early by analyzing behavior across all users, applications and entities.

How AI benefits threat triage

Less false positives with AI

On-prem vs. cloud deployment

Guided threat detection tour
Your DORA Checklist

PostFinance Use Case
DORA, NIS2 & KRITIS Guide
DORA Use Case

Detect APTs: Finance Edition
Monitoring ATM Machines
NIS2 Compliance Checklist
NIS2, DORA & KRITIS Guide
DORA Compliance Checklist
DORA Banking Use Case
NIS2 Manufacturing Use Case
Use Case: Bank in Germany
Success Story: Logistics
Success Story: Banking
Use Case: Manufacturing & NIS2

Success Story: Swiss Hospitals
Use Case: Healthcare & Compliance

Zero Trust in the finance sector

Meeting the unique needs of OT

From patient data to regulatory compliance

Financial sector applications

Made for the industrial world

Secure patient data & compliance

Public security, private data protected

AI against advanced threats

Global Manufacturer WinGD

Public Sector Use Case

Finance & Insurance

Manufacturing & Industrial

Public Sector
Exeon
across industries
Modern environments differ in structure, regulation and risk – but identity-driven threats affect all of them.
Exeon.UEBA provides tailored behavioral visibility for every sector.

Finance & Insurance
Monitor privileged identities and sensitive workflows across core banking, trading, payment and AI-enabled platforms.

Manufacturing & Industrial
Protect production, R&D and engineering systems across hybrid OT/IT environments.

Public Sector
Operate with complete data sovereignty and strict privacy controls. Exeon.UEBA detects identity misuse and privilege escalations...
Frequently asked questions
Discover how Exeon.UEBA delivers unified visibility across your SAP landscape to instantly spot stolen credentials, insider threats, and suspicious transaction activity. Our experts are happy to help with any additional questions.
What is UEBA for SAP and how does Exeon.UEBA work?
User and Entity Behavior Analytics (UEBA) detects cyber threats by learning normal behavior patterns of users, service accounts, and applications in SAP environments. Exeon.UEBA for SAP analyzes SAP Security Audit Logs (SAL) and related system logs to build behavioral baselines for SAP identities, transactions, clients, and tables. It then detects anomalies such as credential misuse, unusual transaction activity, or suspicious data exports that traditional, rigid SAP monitoring often misses. Because Exeon.UEBA processes data in real time using stream-based analytics, it can detect threats immediately while supporting on-premises or air-gapped deployments for full data sovereignty.
What types of SAP security threats can Exeon.UEBA detect?
Exeon.UEBA for SAP detects suspicious behavior across the SAP application layer, including both external attacks and insider threats.
Examples include:
- Stolen SAP credentials used for unusual logins
- Privilege escalation or unauthorized role changes
- (First-time) execution of sensitive SAP transactions
- Access to sensitive SAP tables such as user credential tables
- Abnormal data exports or large table downloads
- Unauthorized debugger use or configuration changes
By monitoring behavioral patterns across SAP identities, transactions, and service accounts, Exeon.UEBA can identify subtle misuse that appears legitimate to traditional security tools.
Which deployment options does Exeon.UEBA for SAP support?
Exeon.UEBA for SAP supports flexible deployment models designed for regulated and security-sensitive environments. Available deployment options include self-hosted deployments either within your own data center or in a private (controlled infrastructure) and support hybrid architectures combining on-prem and cloud systems as well as air-gapped environments with no external connectivity. All deployments keep SAP security data within your controlled infrastructure, supporting compliance with regulations such as GDPR, NIS2, and DORA.
How does Exeon.UEBA protect SAP user and identity data?
Exeon.UEBA includes built-in privacy protection mechanisms to safeguard sensitive identity information during analysis. Identity attributes such as usernames, user IDs, or email addresses can be pseudonymized and sensitive log data content can be encrypted at ingestion. Behavior analytics can then operate on protected data while still maintaining analytical context. This approach enables organizations to perform advanced threat detection while maintaining compliance with privacy regulations and internal data protection policies.
Can Exeon.UEBA detect insider threats in SAP?
Yes. Exeon.UEBA for SAP is designed to detect insider threats and account misuse by identifying abnormal behavior within legitimate SAP activity.
The platform learns typical behavior for each SAP user and service account and alerts on deviations such as:
- Unusual access to sensitive SAP tables
- Unauthorized role or permission changes
- Unexpected execution of administrative transactions
- Suspicious data exports or system configuration changes
Because the system analyzes behavioral patterns rather than relying solely on static rules, it can detect malicious or compromised insiders even when their actions appear technically legitimate.
What is the difference between Exeon.UEBA for SAP and SIEM-based UEBA?
Many SIEM platforms provide UEBA features, but they are often limited by batch processing, rule-based detection, and high SAP log ingestion and data storage costs.
Exeon.UEBA for SAP is purpose-built for behavioral detection and offers several advantages:
- Real-time stream-based analytics instead of batch analysis
- Pre-built SAP detection logic for common misuse scenarios
- Behavioral baselining across SAP users, transactions, and systems
- Smart log normalization that reduces SIEM log volume
This approach improves detection accuracy while lowering operational costs compared to traditional SIEM-centric monitoring
How does Exeon.UEBA ensure data sovereignty for SAP environments?
Exeon.UEBA for SAP is designed for organizations that require full control over their security data.
The platform supports on-premises and air-gapped deployment models so that SAP logs and identity data never need to leave yourinfrastructure. Combined with built-in encryption and pseudonymization capabilities, this allows organizations in regulated industries toperform behavioral threat detection while maintaining strict data sovereignty and privacy compliance.
Does Exeon.UEBA integrate with SIEM, SOAR, or IAM tools?
SIEM-based UEBA is often rule-driven – which need to be manually added and tuned – and limited by batch processing and high data-ingest costs.
Exeon.UEBA uses real-time streaming analytics, smart log pre-processing for decreased data volumes and flexible behavior models to deliver faster, more accurate detection at lower cost.
How quickly can Exeon.UEBA for SAP be deployed?
Yes. Exeon.UEBA integrates easily with existing security operations platforms.
Detected SAP anomalies and behavioral insights can be forwarded to SIEM systems, SOAR platforms, or ticketing tools for centralized monitoring and incident response. Open APIs also enable integration with IAM systems and automated response workflows.
This ensures SAP-specific threats are incorporated into your broader security operations and response processes.
Can Exeon.UEBA be used for other applications besides SAP?
Most organizations achieve meaningful SAP security visibility within days, not months.
Exeon.UEBA can ingest SAP Security Audit Logs (SAL) directly without requiring SAP agents or complex log transformations. Its standardized log modeling and pre-built threat detection capabilities enable rapid onboarding across both on-prem and cloud SAP environments.
This allows security teams to begin detecting abnormal SAP behavior and identity misuse shortly after deployment.
Ready to optimize your SOC?
Your cybersecurity is our priority. Connect with us to discuss how our AI technology enhances protection, boosts efficiency, and reduces costs.
