Black Hat 2025: More Attacks, More Tools – and Why That Doesn’t Automatically Mean More Security

Black Hat is an annual stage for both offensive innovation and new defensive thinking, ranging from zero-click Apple exploits to BIOS malware designed to outlive any OS defenses.
SIEM vs. NDR: Who is improving modern SOCs?
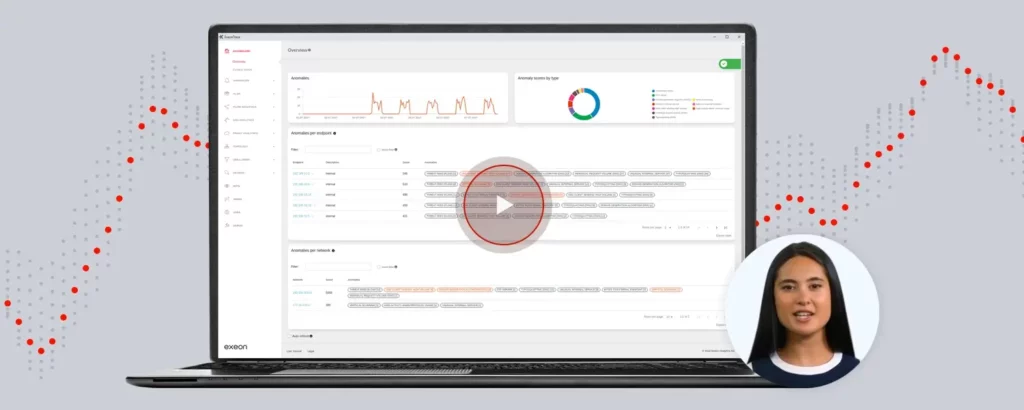
How Network Detection and Response enhances SOCs with advanced threat detection, cost efficiency, and scalability. Watch the recording on how to extend the effectiveness of your SOC.
Incident Response in Cybersecurity
Why Companies Should Focus on Prevention and Detection First Cyberspace threats are constantly increasing, and cyberattacks have considerable financial consequences. The average damage from a data breach in 2024 was around USD 4.88 million, an increase of 10% compared to the previous year (IBM Breach Report 2024). Companies must invest in robust cyber defense; incident […]
Best-of-Breed Done Right

Why a multi-vendor approach is a secure idea What is Best-of-Breed? In the context of cyber security, a best-of-breed approach involves selecting the most effective security tools from different vendors to address specific security needs comprehensively. It aims to achieve optimal performance by combining specialized solutions that excel in their respective areas, thus creating a […]
A Wrap-Up of 07-19
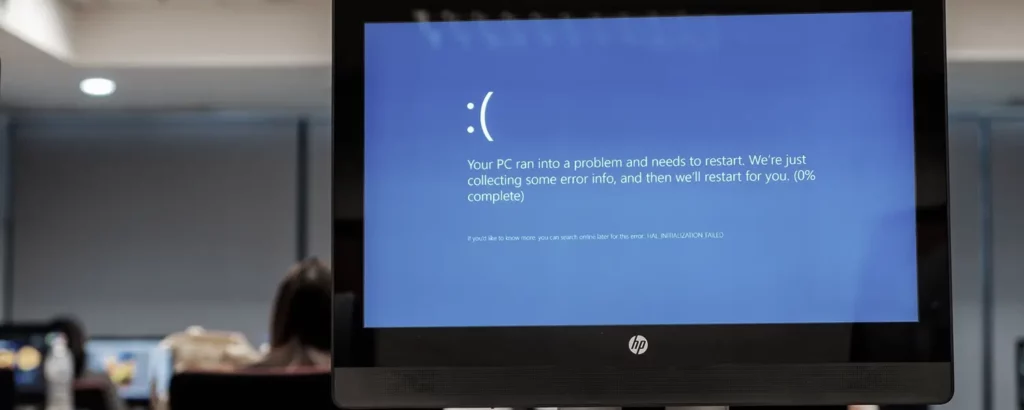
Executive Summary Intro A faulty update published by CrowdStrike caused massive global IT outages last Friday, affecting numerous industries and critical infrastructures. Approximately 8.5 million Windows devices worldwide were impacted, according to Microsoft. Airports, banks, healthcare facilities, and government institutions were significantly affected, with the full extent of the consequences still unknown. Cybercriminals attempted to […]
Obfuscation: Good to Protect, Hard to Detect
What is Obfuscation? Obfuscation is an important technique for protecting software, but it also carries risks, especially when used by malware authors. We took a closer look: Obfuscation refers to the technique of deliberately making information difficult to understand, especially in the realm of computer code. An important area of obfuscation is data obfuscation, where sensitive data is […]
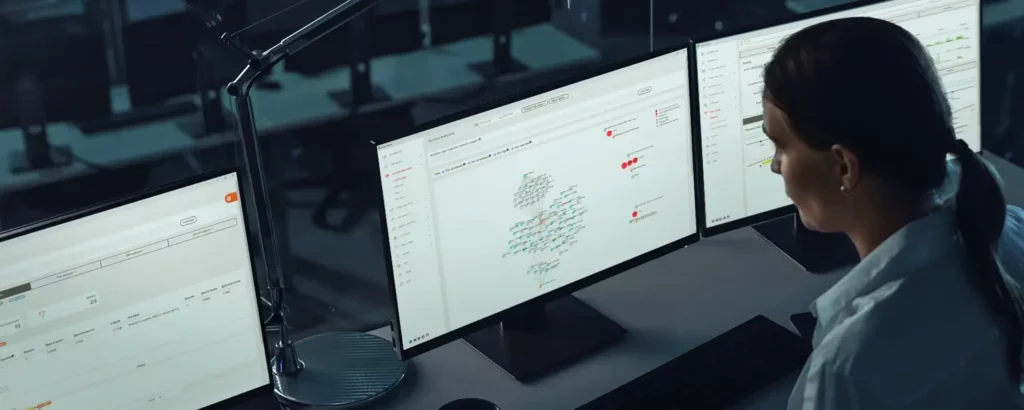
SOC Visibility Triad & the Role of NDR Solutions

How the SOC Visibility Triad enhances threat detection by combining SIEM, NDR, and EDR for stronger cybersecurity, and what specific aspects are to consider for holistic IT security.
How to Detect the Exploitation of Network Device Vulnerabilities

In this article, we share some ideas on how to detect and hunt the exploitation (meaning the abuse) of network device vulnerabilities and how Network Detection and Response (NDR) supports such analysis. When working in cybersecurity, you are familiar with the following headline: Vulnerability XY on product Z may allow an unauthenticated user to execute unauthorized code […]