Black Hat 2025: More Attacks, More Tools – and Why That Doesn’t Automatically Mean More Security

Black Hat is an annual stage for both offensive innovation and new defensive thinking, ranging from zero-click Apple exploits to BIOS malware designed to outlive any OS defenses.
SIEM vs. NDR: Who is improving modern SOCs?
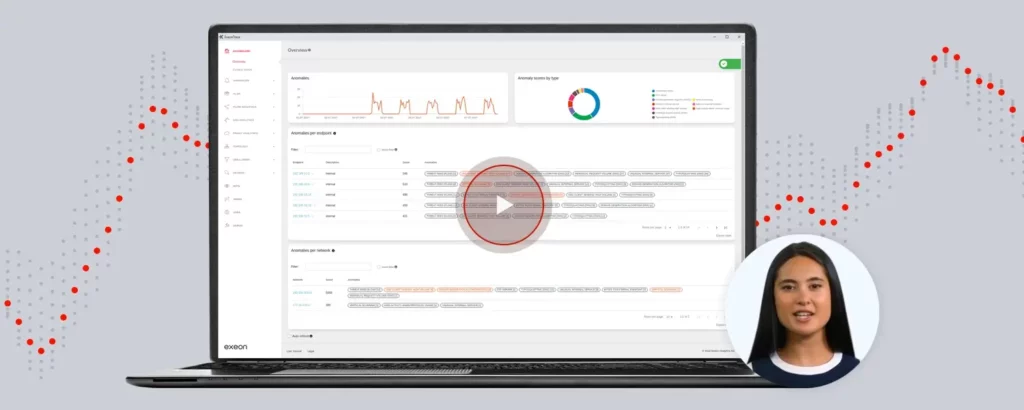
How Network Detection and Response enhances SOCs with advanced threat detection, cost efficiency, and scalability. Watch the recording on how to extend the effectiveness of your SOC.
How to Monitor & Stop Supply Chain Attacks

A supply chain attack is a type of cyberattack that targets the software or hardware supply chain. Instead of directly attacking a target organization, the attacker focuses on compromising the suppliers or vendors associated with the target. This approach allows the attacker to infiltrate the target organization indirectly, often exploiting trust in the supply chain. […]
Cloud Security vs On-Premises

While cloud solutions often offer strong security, some opt for on-prem systems for greater control, performance, offline reliability & more.
Octo2: The Evolution of A Dangerous Malware Family

(image generated via DALL·E) The Octo (ExobotCompact) malware family has become the dominant threat in the cyber security landscape. The release of Octo2, an evolved variant, demonstrates the increasing sophistication of modern malware. Octo2 targets Android devices and uses Domain Generation Algorithms (DGA) to generate dynamic Command and Control (C2) servers, making detection much more difficult. […]
Allianz Risk Barometer: Heightened Alarm on Cyber Threats

Based on the Allianz Risk Barometer results, how can you best protect your organization from cyber-attacks? Here are robust, future-proof cybersecurity measures and why management needs to be involved.
Akira Ransomware: How to Protect Your Business
The Akira ransomware group quickly gained notoriety. The group emerged in March 2023 and is already the fourth most active group worldwide. If they keep up with this speed, they will be surpassing Lockbit soon, demanding millions in ransom from its victims. Akira mainly targets companies in various industries, including public, finance, real estate, manufacturing, […]
How to Catch Data Exfiltration with Machine Learning
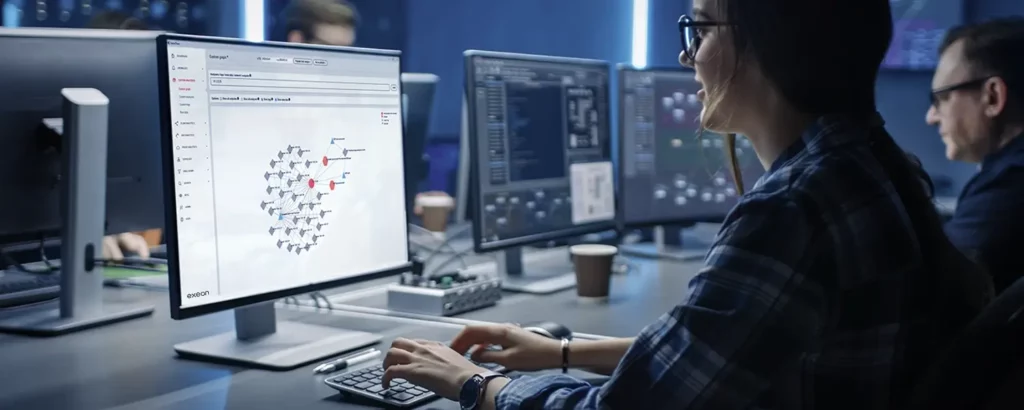
Why is Detecting Data Exfiltration So Important? In today’s landscape, there is an unprecedented surge in ransomware attacks and data breaches aimed at coercing businesses. Concurrently, the cybersecurity industry is confronted with numerous critical vulnerabilities within database software and corporate websites. These developments paint a grim picture of data exposure and unauthorized data removal that security leaders […]
Machine Learning Algorithms from a Detection Engineers’ Perspective
Detection engineers navigate unique scenarios when building detections, in addition to the challenges of new, complex threats. This blog explores both from their perspective and key questions that arise during use case development.
How Network Detection and Response (NDR) Fills the Security Gaps of Intrusion Prevention Systems (IPS)

In order to identify and prevent threats, IPS relies on signature-based detection. However, this can cause various blind spots and weaknesses in network protection. NDR can overcome these drawbacks for more reliable and holistic protection against intrusions.