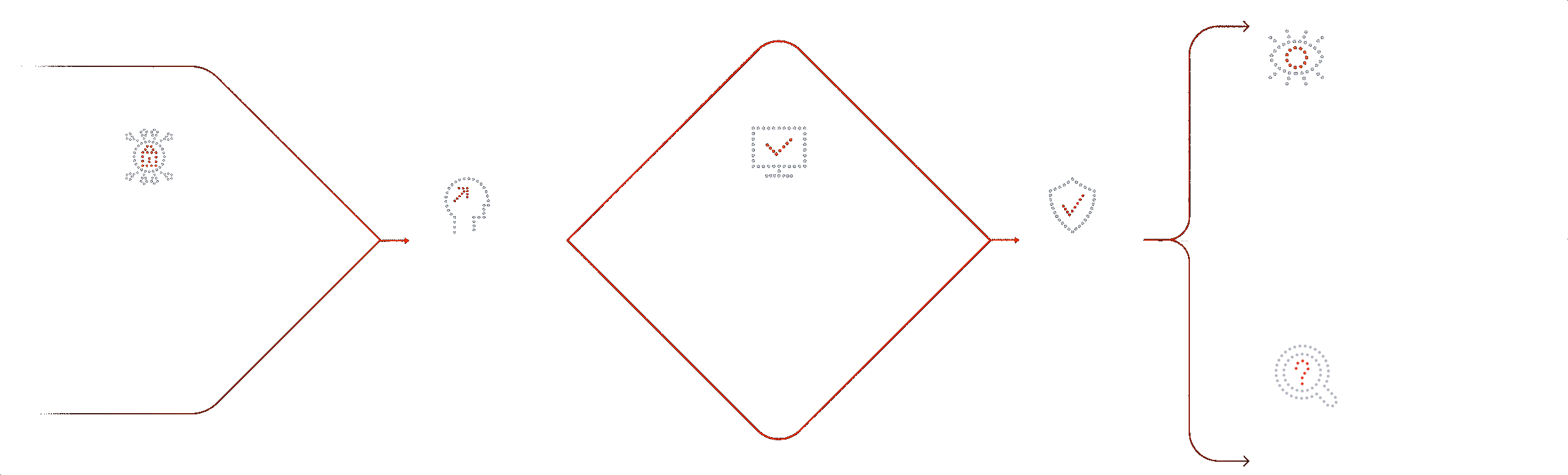
Continuous Network Visibility & Asset Intelligence - built on the analytics foundation of Exeon.NDR
Fast. Agentless. Sensor-free.
Turn raw network logs into a unified, actionable view of assets, traffic, and dependencies – across IT, OT, IoT, cloud, and on-prem.










Exeon.Visibility applied to real world challenges
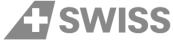
Lack of Visibility
No single view of traffic and assets. Traditional monitoring loses sight with TLS 1.3 encryption.
Fragmented Environments
IT, OT, and IoT are monitored in isolation – disconnected on-prem, cloud and virtual landscapes.
Introducing Zero Trust
No clear asset and traffic baselines for segmentation – incomplete insight to verify Zero Trust enforcement.
Unknown assets and services
Shadow IT and legacy systems persist and unauthorized services stay invisible.
The Exeon.Visibility advantage
Holistic central view
Consistent visibility, everywhere logs exist. TLS 1.3 ready by design – without decryption.
Unified hybrid visibility
Consolidated view across on-prem, cloud or virtual environments - no silos between IT, OT, and IoT landscapes.
Zero Trust Enablement
Asset and traffic baselines for segmentation and ZTNA. Continuous monitoring to validate Zero Trust controls.
Asset & service transparency
Complete inventory of devices & flows. Exeon.Visibility understands system & service relationships.
Why Exeon.Visibility

Traffic visualization
Unified visibility across hybrid and decentralized infrastructures, unaffected by encrypted traffic.
Policy enforcement monitoring
Highlights policy violations and unexpected communication patterns to support compliance and network hygiene.
Shadow IT recognition
Automatically uncovers unauthorized apps, cloud services, or unmanaged devices to reduce risk.
Log-based network insights
Leverage your existing network logs for instant visibility – no agents, no sensors, no infrastructure changes.
Data sovereignty
Keeping all data within the customer’s secure and controlled environments (private, cloud, or on-prem).
Expandable threat detection
Built on the same analytics foundation as Exeon.NDR, enabling seamless activation of AI-based detection capabilities when required.
Exeon compared
Exeon eliminates the challenges of deep packet inspection (DPI) via agentless, metadata monitoring with open APIs for scalable log and flow ingestion, transparent custom detection, SOAR/SIEM‑optimized responses, and more.
Capabilities
Lightweight, efficient data analysis without traffic mirroring or sensors
Security analytics unaffected by encryption
Superior network visibility, not restricted to core switch traffic only
Fully on-prem data processing
Transparent Machine Learning models
Exeon
Vectra
Darktrace
ExtraHop
Book a demo.
Precision and excellence into one product: experience the power of metadata analysis with our experts.
Real-world success stories
Here’s how we provide our unique AI-powered technology to support security teams and managed security service providers in safeguarding corporate and personal data, operations, and reputation.

Network & Security Engineer, Solothurner Spitäler
“Exeon is our cybersecurity alarm system, alerting us to any network anomalies. What also really convinced us is the platform’s intuitive interface—it has become a tool to reliably monitor and secure our data and network.”

CISO, SWISS International Airlines
“As the Swiss national airline, we are driven by a passion for exceptional performance, in the spirit of our guiding principles. A stable and secure IT is the most important basis for an excellent customer service. For the security of SWISS IT, we use Exeon as a central cybersecurity tool, fully managed by our long-term partner Reist Telecom AG. A perfect combination and solution to monitor our network and quickly detect any kind of anomalies.”

ICT Project Leader, WinGD
“Exeon provides us with complete visibility of our network data flows and automatically detects suspicious behavior. Thanks to their AI algorithms, we immediately identify potential cyber threats and can respond quickly and efficiently. This way, we prevent attackers from moving undetected in our systems, infiltrating the infrastructure, or bypassing existing security measures.”

Regional Practice Head, Wipro
“Exeon is the ideal solution for transitioning from a legacy SOC to a Next-Generation SOC. It enhances detection capabilities, minimizes alert noise, and significantly reduces costs.”

Director of Cybersecurity Research, KuppingerCole
“The management and analyst interfaces are intuitive and can yield important insights for customers. Exeon’s approach to data retention helps customers keep data local for regulatory compliance and reduces costs for long-term storage by only retaining event metadata. The solution supports the most pertinent standards for exchanging threat information.”
Frequently asked questions
Learn how Exeon.Visibility empowers your IT and network team with real time network insights to bring back visibility, discover security vulnerabilities and detect policy violations. Our experts are happy to help with any additional questions.
Why do organizations need Exeon.Visibility for network visibility and asset inventory?
Modern IT, OT, and cloud environments lack a single, reliable source of truth for assets and network communications. Exeon.Visibility provides continuous network visibility and automated asset discovery by analyzing existing network logs. This enables organizations to build an accurate asset inventory, understand traffic patterns, and establish the foundation required for Zero Trust policies, segmentation, and compliance – without deploying agents or sensors.
How does Exeon.Visibility support asset inventory for Zero Trust implementation and network segmentation?
Exeon.Visibility continuously discovers all communicating devices, services, and dependencies across IT, OT, IoT, cloud, and on-prem environments. By mapping real traffic flows, it establishes asset and communication baselines that are essential for Zero Trust Network Access (ZTNA), segmentation planning, and policy definition. This visibility allows teams to design and validate Zero Trust policies based on actual behavior rather than assumptions.
Can Exeon.Visibility unify asset management across IT, IoT and OT environments?
Yes. Exeon.Visibility provides a unified view of assets and communications across converged IT, IoT and OT landscapes. By automatically discovering and monitoring assets like network, security, and cloud systems, it eliminates silos between IT, IoT and OT teams and reveals unmanaged, legacy, or shadow systems that are often missing from traditional asset management tools.
How does Exeon.Visibility create a single pane of glass across on-prem and cloud networks?
Exeon.Visibility aggregates and normalizes network logs from on-premises infrastructure, virtualized environments, and public clouds (including AWS, Azure, and Google Cloud). All traffic, assets, and dependencies are represented in a single, consistent data model, delivering centralized visibility across hybrid and distributed environments – without blind spots caused by encryption or platform boundaries.
Is Exeon.Visibility able to analyze log data from Google Cloud Platform (GCP) ?
Exeon.Visibility can process this log data. It is fully capable of analyzing traffic flowing into, within and out of Azure, AWS and the Google cloud, providing full visibility into what is happening within the cloud.
What is the difference between Exeon.Visibility and Exeon.NDR?
Exeon.Visibility focuses on continuous network visibility, asset discovery, dependency mapping, and policy insight through analytics and visualization. Exeon.NDR builds on the same data foundation and adds advanced machine-learning-based threat detection and response capabilities. Organizations can start with Exeon.Visibility and seamlessly upgrade to Exeon.NDR when advanced detection is required.
Which deployment options does Exeon.Visibility support for regulated environments?
Exeon.Visibility supports on-premises or self-hosted as well as private or public cloud deployments. By default, all data remains within the customer’s controlled environment, ensuring data sovereignty and compliance with regulatory requirements such as NIS2, DORA, and GDPR. No data needs to be sent to external SaaS platforms.
Factsheet
Learn how Exeon.Visibility safeguards your IT network. Our subscription includes the software license, setup, training, and expert support. Pricing is tailored to your analysis needs and the number of active internal IPs.
Talk to an expert
Let’s discuss your specific requirements – get in touch with us today to learn more about our NDR solution or to discuss your security needs.