Swiss-Engineered AI to Strengthen Resilience
After over a decade of institutional research, we have engineered sophisticated AI to empower security teams with unmatched precision, speed and efficiency in their daily operations.

How AI empowers security teams
Return on Investment through efficient threat detection and reduced response times with AI (Forrester®)
Faster incident response through AI automation (Gartner®)
Reduction in false alarms with precise, machine learning-based detection (Gartner®)
Security teams must focus on real threats. That’s why AI and machine learning are the keys to becoming faster and more precise.
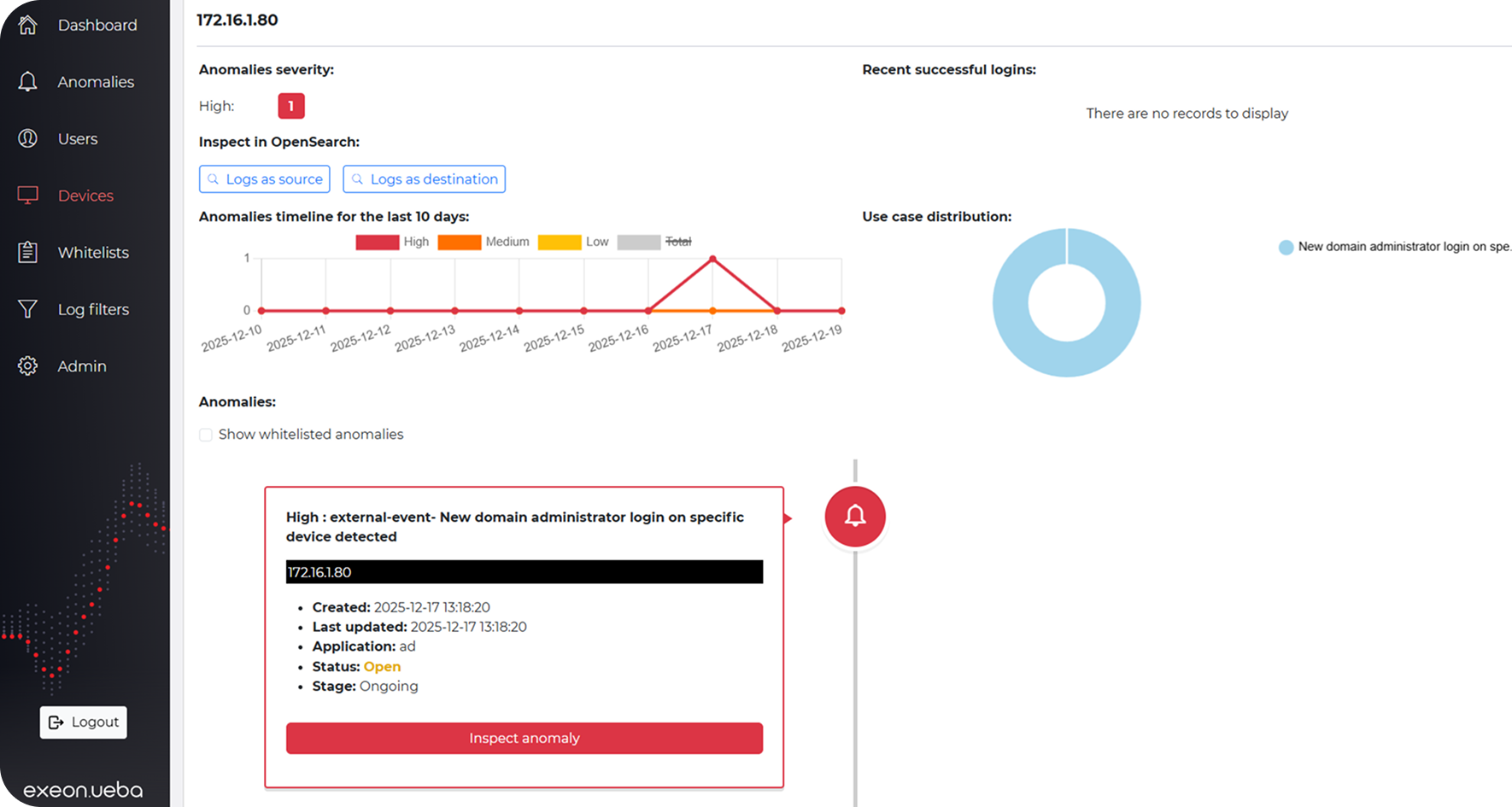
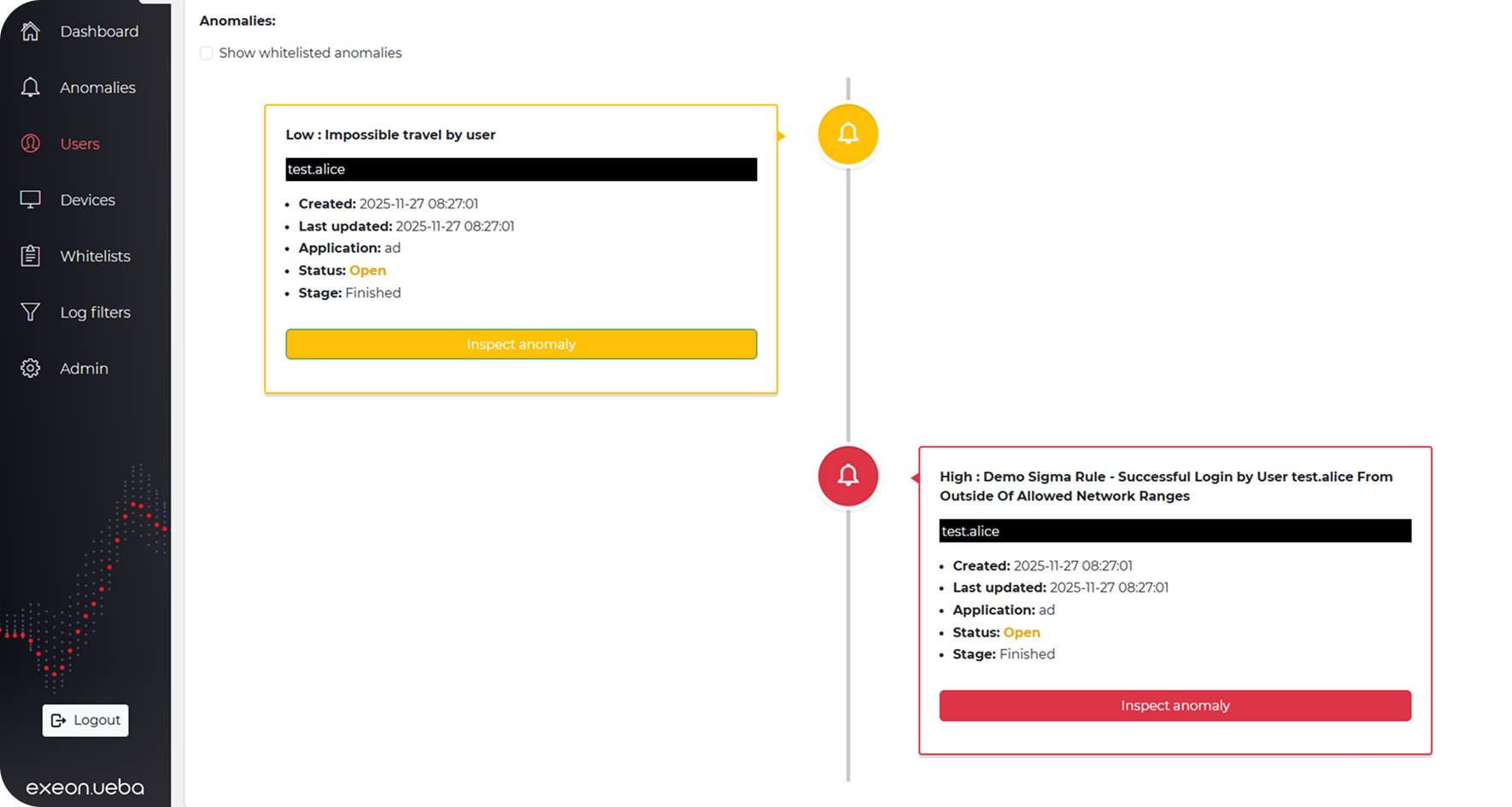
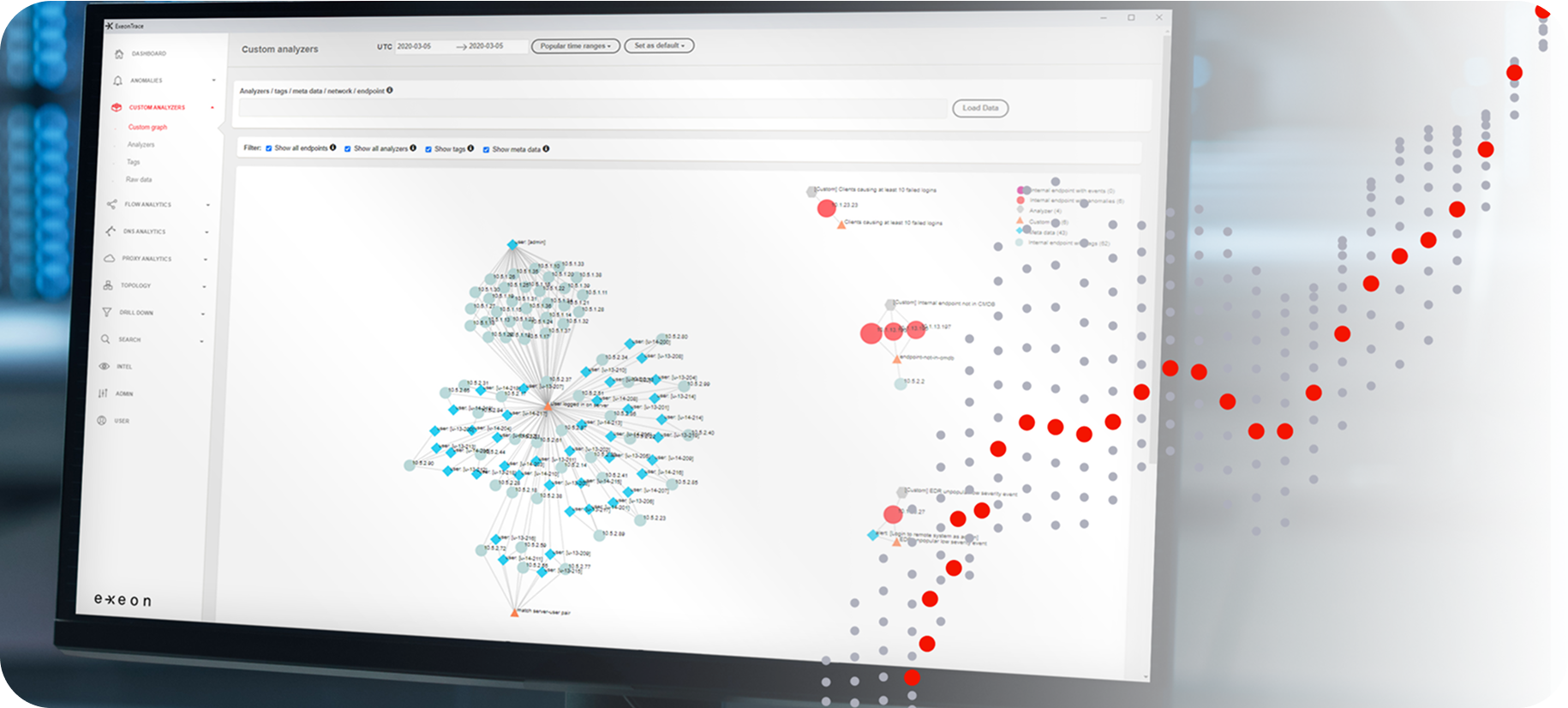
Monitor with surgical precision
Exeon's AI-driven metadata analysis and a clever whitelisting, filters safe traffic, eliminates false positives, and surfaces true anomalies across IT and OT.
Detect threats in billions of activities
Machine learning behavioral models analyze network traffic to identify known attack patterns and previously unseen anomalies for early, effective threat detection.
Automate rapidresponse
Risk-scored alerts flow into your SOAR platform via open APIs, where playbooks isolate hosts and block malicious traffic in seconds.
Supervised machine learning
Supervised models are pretrained on real-world attack patterns in controlled environments, enabling accurate, out-of-the-box detection for known threats from day one.
Unsupervised algorithms
Unsupervised algorithms learn typical behavior onsite, identifying anomalies unique to each environment in real-time without prior labeling or rules.
Expert use case integration
Expert use case integration correlates traditional indicators with network data, enriching detection algorithms with additional context for superior accuracy.
Risk-based alerting
Risk-based alerting and dynamic scoring mechanisms evaluate the severity and context of each incident, enabling security teams to triage effectively and focus response efforts on the most impactful threats.
No deep packet inspection (DPI)
Exeon analyzes metadata, not payloads, ensuring encrypted traffic remains private while maintaining full visibility into behavioral anomalies.
Unified visibility across identities & applications
Monitor all users, entities, apps, APIs, AI agents and legacy systems.
Dual detection: Expert use cases + adaptive AI
Expert-crafted logic is combined with learning-based models to detect subtle anomalies with high accuracy.
Real-time stream processing for instant detection
A high-performance streaming engine, delivering instant alerts also when processing billions of data points.
Efficient processing for reduced volume & cost
Deduplication, compression and normalization cut log volume and SIEM costs while improving detection efficiency.
Flexible log onboarding for any application
Standardized log modelling enables fast integration of SaaS, on-prem and custom apps.
Trusted by global organizations













Market comparison
Exeon eliminates DPI’s challenges with its innovative metadata analysis approach, delivering real-time insights across physical, virtual, and cloud environments without invasive methods.
Capabilities
Lightweight, efficient data analysis without traffic mirroring or sensors
Security analytics unaffected by encryption
Superior network visibility, not restricted to core switch traffic only
Powerful Machine Learning algorithms
Fully on-prem data processing
Exeon
Vectra
Darktrace
ExtraHop
Security installations

IT / OT / IoT
It enables real-time threat detection, automated response, and threat hunting, reduces false positives, and empowers security teams to protect critical infrastructure with greater efficiency and precision.
- Real-time threat & anomaly detection
- Automated incident response and faster mitigation
- Supporting proactive threat hunting

SOC+
AI strengthens SOCs by automating threat detection, accelerating response times, and enhancing decision-making accuracy.
- Faster identification of threats
- Reduced workload by incident prioritization
- Increased accuracy when identifying complex attack patterns
Data Security
AI enhances data security by automating threat detection, improving data protection, and enabling faster responses to breaches.
- Real-time detection of data breaches
- Automated responses to mitigate threats quickly
- Enhanced protection against complex threats

Insider Threat Management
A multi-layered approach to detect and mitigate insider threats by leveraging AI-powered Network Detection and User and Entity Behavior Analytics.
- Comprehensive monitoring for full network and application visibility
- Zero Trust integration to enforce strict access controls
- Real-time security insights via live dashboards
AI & Security Use Cases
Our technology is engineered to adapt to business specifications and individual requirements without compromising security, efficiency, and compliance.

Public Sector Use Case

AI against advanced threats

Guided threat detection tour

On-prem vs. cloud deployment

Less false positives with AI

How AI benefits threat triage
What customers say about our AI technology
Security teams of global organizations report on their experience with our AI and machine learning.

CISO, SWISS International Airlines
“As the Swiss national airline, we are driven by a passion for exceptional performance, in the spirit of our guiding principles. A stable and secure IT is the most important basis for an excellent customer service. For the security of SWISS IT, we use Exeon as a central cybersecurity tool, fully managed by our long-term partner Reist Telecom AG. A perfect combination and solution to monitor our network and quickly detect any kind of anomalies.”

Head IT Security, PostFinance AG
“PostFinance has chosen Exeon.NDR because of its open and future-proof architecture. Not needing any hardware sensors and being able to control data flows, we didn’t have to make any significant changes to our existing infrastructure. We are also convinced by the cooperation with the competent and technically outstanding Exeon team.”

CEO & Founder, Planzer
“As CEO and owner of a fast moving, international logistics company, I cannot afford any system interruptions due to cyber incidents. With Exeon.NDR, we have found a Swiss solution to monitor our network and quickly detect cyber threats.”

Head Infrastructure & Applications, 3 Banken IT
“We especially appreciate the comprehensive network visibility that Exeon.NDR offers us.
The anomaly detection is also extremely accurate and allows our analysts to focus on the essential threats.”

Director of Cybersecurity Research, KuppingerCole
“The management and analyst interfaces are intuitive and can yield important insights for customers. Exeon’s approach to data retention helps customers keep data local for regulatory compliance and reduces costs for long-term storage by only retaining event metadata. The solution supports the most pertinent standards for exchanging threat information.”

Network & Security Engineer, Solothurner Spitäler
“Exeon is our cybersecurity alarm system, alerting us to any network anomalies. What also really convinced us is the product’s intuitive interface – it has become a tool to reliably monitor and secure our data and network.”

ICT Project Leader, WinGD
“Exeon provides us with complete visibility of our network data flows and automatically detects suspicious behavior. Thanks to their AI algorithms, we immediately identify potential cyber threats and can respond quickly and efficiently. This way, we prevent attackers from moving undetected in our systems, infiltrating the infrastructure, or bypassing existing security measures.”

Senior Product Portfolio Manager Cyber Defense, Swisscom
“Exeon offers numerous functional advantages over competing NDR products. With Exeon, we have the ability to leverage innovative technologies and advanced analytics to provide our customers with a best-in-class security solution. Together, we are committed to improving the security landscape.”

Regional Practice Head, Wipro
“Exeon is the ideal solution for transitioning from a legacy SOC to a Next-Generation SOC. It enhances detection capabilities, minimizes alert noise, and significantly reduces costs.”

CEO, Real Security
“As leading distributors, we’re always on the lookout for reliable, innovative, and powerful solutions to strengthen our portfolio and shape the future of cybersecurity. Exeon has proven time and again to be a trustworthy and easy-to-work-with partner. Their solution, exeon.ndr, has already made a big impact across various sectors.”
Industry-focused, results-driven
Use Case: Bank in Germany
DORA compliance, tackling threats like APTs & ransomware, improved threat detection, and faster response times.
Success Story: Logistics
Fast-moving, international logistics company defeats system interruptions from cyber incidents with Exeon.NDR.
Success Story: Banking
A cybersecurity case study on PostFinance, one of Switzerland’s leading retail financial institutions.
Use Case: Manufacturing & NIS2
OT/IIoT integration and compliance: how a mechanical engineering company increases their cybersecurity posture.

Success Story: Swiss Hospitals
Read how our product became an integral security monitoring tool to safeguard Solothurner Spitäler’s IT & OT networks.
Use Case: Healthcare & Compliance
Centralized visibility and monitoring of hybrid environments to safeguard critical medical systems.

Global Manufacturer WinGD
In this video testimonial, our customer WinGD explains how Exeon.NDR strengthens their cybersecurity.
Frequently asked questions
Further details on our product’s powerful machine learning algorithms designed to detect sophisticated cyber threats by analyzing your log data.
How is supervised machine learning used in Exeon products?
Supervised machine learning in Exeon products is trained on labeled datasets, meaning it’s trained from past attacks and predefined threat patterns. This approach is particularly effective for detecting known threats, such as lateral movement or brute-force attacks. As for unsupervised ML, by matching current network activity with historical attack data, it quickly identifies suspicious behavior that fits previously seen attack signatures. For example, Exeon.NDR can detect command-and-control traffic based on patterns found in past attack logs, enabling security teams to respond swiftly.
How is unsupervised machine learning used in Exeon products?
Unsupervised machine learning, on the other hand, does not rely on predefined patterns but instead identifies unknown or evolving attack patterns. It analyzes network behavior and flags anomalies that do not conform to normal activity. This makes it particularly useful for detecting new and sophisticated threats, such as zero-day attacks or advanced persistent threats (APTs). In Exeon products, this capability helps uncover subtle attacker movements within a network, such as lateral movement, where an intruder spreads from one system to another while avoiding traditional detection methods.
Why do we use both supervised and unsupervised?
By combining supervised and unsupervised machine learning, we ensures a comprehensive security approach. Supervised learning allows for quick detection of known attack methods, providing immediate protection against familiar threats. At the same time, unsupervised learning enhances security by identifying novel or stealthy attacks that would otherwise go unnoticed. This dual approach maximizes detection accuracy while maintaining adaptability to evolving cyber threats.
What is the future of AI-powered cybersecurity?
The future lies in privacy-conscious security solutions that prioritize detecting threats through intelligent pattern analysis rather than invasive surveillance, ensuring strong protection without overstepping privacy boundaries.
How does behavior-based security enhance protection?
By focusing on network behavior rather than individual data packets, AI-driven security solutions can detect zero-day attacks and unknown threats based on deviations from normal patterns, offering stronger, privacy-friendly protection.
Talk to an expert
Have questions about AI-driven security that is future-proof and scales infinitely? Our experts are available to assist with strategic planning, network security, integrations, and more.
