Best-of-Breed Done Right

Why a multi-vendor approach is a secure idea What is Best-of-Breed? In the context of cyber security, a best-of-breed approach involves selecting the most effective security tools from different vendors to address specific security needs comprehensively. It aims to achieve optimal performance by combining specialized solutions that excel in their respective areas, thus creating a […]
A Wrap-Up of 07-19
Executive Summary Intro A faulty update published by CrowdStrike caused massive global IT outages last Friday, affecting numerous industries and critical infrastructures. Approximately 8.5 million Windows devices worldwide were impacted, according to Microsoft. Airports, banks, healthcare facilities, and government institutions were significantly affected, with the full extent of the consequences still unknown. Cybercriminals attempted to […]
Akira Ransomware: How to Protect Your Business
The Akira ransomware group quickly gained notoriety. The group emerged in March 2023 and is already the fourth most active group worldwide. If they keep up with this speed, they will be surpassing Lockbit soon, demanding millions in ransom from its victims. Akira mainly targets companies in various industries, including public, finance, real estate, manufacturing, […]
Air-Gapping: Not Only Love Is in the Air

Can Air-Gapping Alone Improve Cybersecurity for Critical Industries? Air-gapping is a security measure designed to isolate digital assets and networks from outside connections, to protect against hackers, malware, and other threats by creating an impenetrable barrier. It has its merits, but it has its security issues too, and for a cybersecurity solution to deploy, it needs […]
Obfuscation: Good to Protect, Hard to Detect
What is Obfuscation? Obfuscation is an important technique for protecting software, but it also carries risks, especially when used by malware authors. We took a closer look: Obfuscation refers to the technique of deliberately making information difficult to understand, especially in the realm of computer code. An important area of obfuscation is data obfuscation, where sensitive data is […]
How to Catch Data Exfiltration with Machine Learning
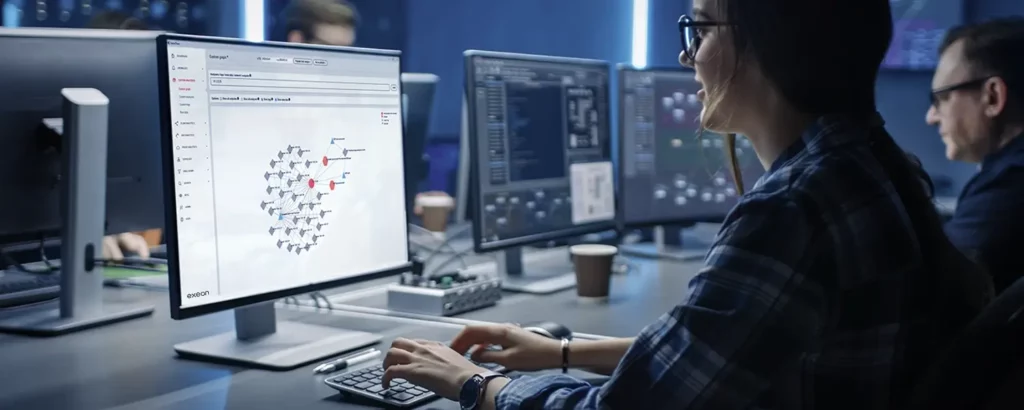
Why is Detecting Data Exfiltration So Important? In today’s landscape, there is an unprecedented surge in ransomware attacks and data breaches aimed at coercing businesses. Concurrently, the cybersecurity industry is confronted with numerous critical vulnerabilities within database software and corporate websites. These developments paint a grim picture of data exposure and unauthorized data removal that security leaders […]
Deep Packet Inspection vs. Metadata Analysis

As encrypted traffic soars and networks grow more complex, traditional Deep Packet Inspection (DPI) struggles. Enter metadata analysis — a lightweight, scalable, and encryption-proof solution powering the next generation of Network Detection and Response (NDR).
Why Zero Trust and Compliance Go Hand in Hand

Pairing Zero Trust with compliance frameworks like NIS2, GDPR, and HIPAA is essential. By integrating strict access controls, continuous monitoring, and advanced tools like Network Detection and Response (NDR), organizations boost their cyber resilience while aligning with legal requirements.
Machine Learning Algorithms from a Detection Engineers’ Perspective
Detection engineers navigate unique scenarios when building detections, in addition to the challenges of new, complex threats. This blog explores both from their perspective and key questions that arise during use case development.
How Network Detection and Response (NDR) Fills the Security Gaps of Intrusion Prevention Systems (IPS)

In order to identify and prevent threats, IPS relies on signature-based detection. However, this can cause various blind spots and weaknesses in network protection. NDR can overcome these drawbacks for more reliable and holistic protection against intrusions.
