Exeon Helps Joint Blue Team Secure 2nd Place at Locked Shields 2026

Exeon at Locked Shields 2026: Testing NDR where it matters most Organized annually by the NATO Cooperative Cyber Defence Centre of Excellence (CCDCOE), Locked Shields is the world’s largest live-fire cyber defence exercise. 41 nations, thousands of participants, and coordinated cyberattacks executed in real time against teams defending critical national infrastructure. There is no safety net. The attacks […]
IoT Security: Closing the Detection Gap

Facing rising cyber risks, industrial infrastructure needs unified defenses: metadata visibility, behavioral detection, and SOC integration—for true resilience.
Black Hat 2025: More Attacks, More Tools – and Why That Doesn’t Automatically Mean More Security

Black Hat is an annual stage for both offensive innovation and new defensive thinking, ranging from zero-click Apple exploits to BIOS malware designed to outlive any OS defenses.
SIEM vs. NDR: Who is improving modern SOCs?
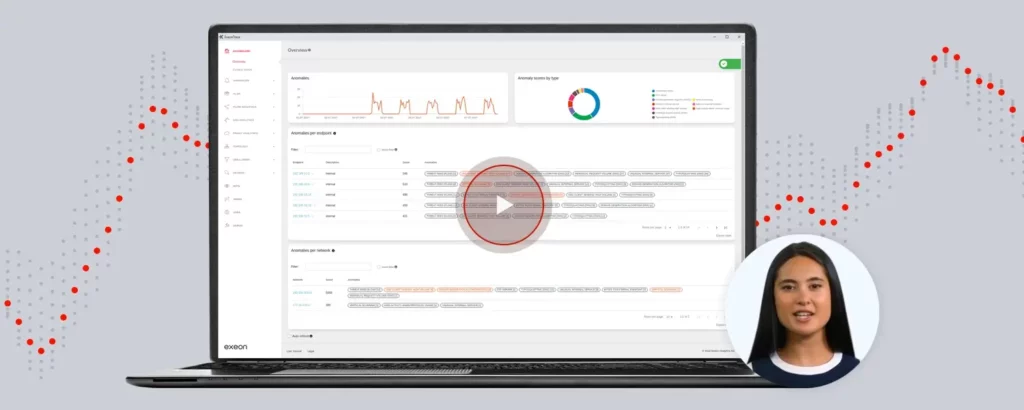
How Network Detection and Response enhances SOCs with advanced threat detection, cost efficiency, and scalability. Watch the recording on how to extend the effectiveness of your SOC.
(Ab)using DLL Sideloading: How to Detect This Growing Threat

What is DLL sideloading? DLL sideloading exploits how Windows applications handle Dynamic Link Library (DLL) files. When a program loads a DLL, it searches for the required file in specific directories. Attackers exploit this behavior by placing a malicious DLL in the same directory as the executable and tricking the application into loading the malicious […]
How to Monitor & Stop Supply Chain Attacks

A supply chain attack is a type of cyberattack that targets the software or hardware supply chain. Instead of directly attacking a target organization, the attacker focuses on compromising the suppliers or vendors associated with the target. This approach allows the attacker to infiltrate the target organization indirectly, often exploiting trust in the supply chain. […]
Cloud Security vs On-Premises

While cloud solutions often offer strong security, some opt for on-prem systems for greater control, performance, offline reliability & more.
Octo2: The Evolution of A Dangerous Malware Family

(image generated via DALL·E) The Octo (ExobotCompact) malware family has become the dominant threat in the cyber security landscape. The release of Octo2, an evolved variant, demonstrates the increasing sophistication of modern malware. Octo2 targets Android devices and uses Domain Generation Algorithms (DGA) to generate dynamic Command and Control (C2) servers, making detection much more difficult. […]
Incident Response in Cybersecurity
Why Companies Should Focus on Prevention and Detection First Cyberspace threats are constantly increasing, and cyberattacks have considerable financial consequences. The average damage from a data breach in 2024 was around USD 4.88 million, an increase of 10% compared to the previous year (IBM Breach Report 2024). Companies must invest in robust cyber defense; incident […]
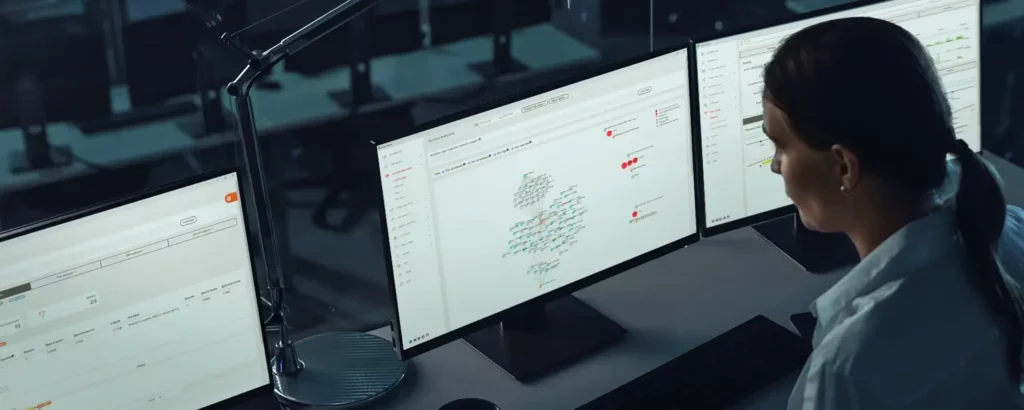
Major SOC Mistakes and How You Can Avoid Them
For many organizations, an in-house or managed security operations center (SOC) plays a critical role in monitoring and defending against cyber threats. It is essential for organizations because it provides continuous monitoring, rapid threat detection, and effective response to protect against attacks. Its proactive approach enhances cybersecurity by identifying and mitigating potential risks, ensuring the […]
