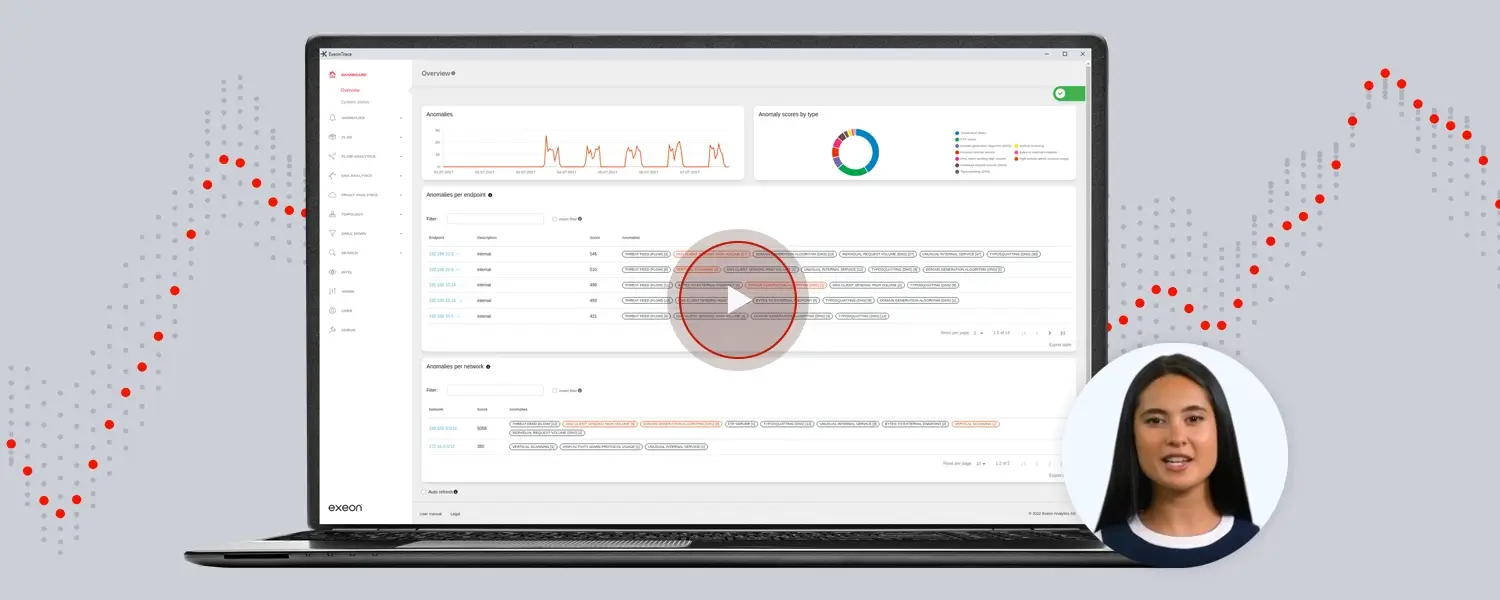
Empowering Next-Gen SOC Capabilities
Exeon.NDR + UEBA enhance existing SOC operations with AI-driven detection, behavioral analytics, and rich network telemetry – empowering playbook execution, reduced dwell time, and strong cyber resilience.
SOC challenges today
of critical SOC alerts go uninvestigated.
alert volumes, false positives, and repetitive triage reduce the SOC’s effectiveness and increase the risk of missed threats.
current gap of cybersecurity workers, making automated & AI-based detection vital.
What Exeon’s technology solves
Exeon turns SOCs into proactive, AI-powered defense hubs by addressing key security challenges.
Lack of automation
SOC teams face manual investigations, slowing down responses, with SIEMs generating over 10,000 alerts/day (50% being redundant or irrelevant).
Siloed IT & OT security
Traditional tools seldom span both networks, leaving blind spots in critical infrastructure. Exeon merges IT, OT and IoT telemetry in a single graph for fast, context-rich detection.
Fragmented hybrid-cloud operations
Multicloud growth strains legacy SIEMs; our cloud-native collectors scale across AWS, Azure, GCP and on-prem with one ruleset, sustaining 30% faster incident resolution.
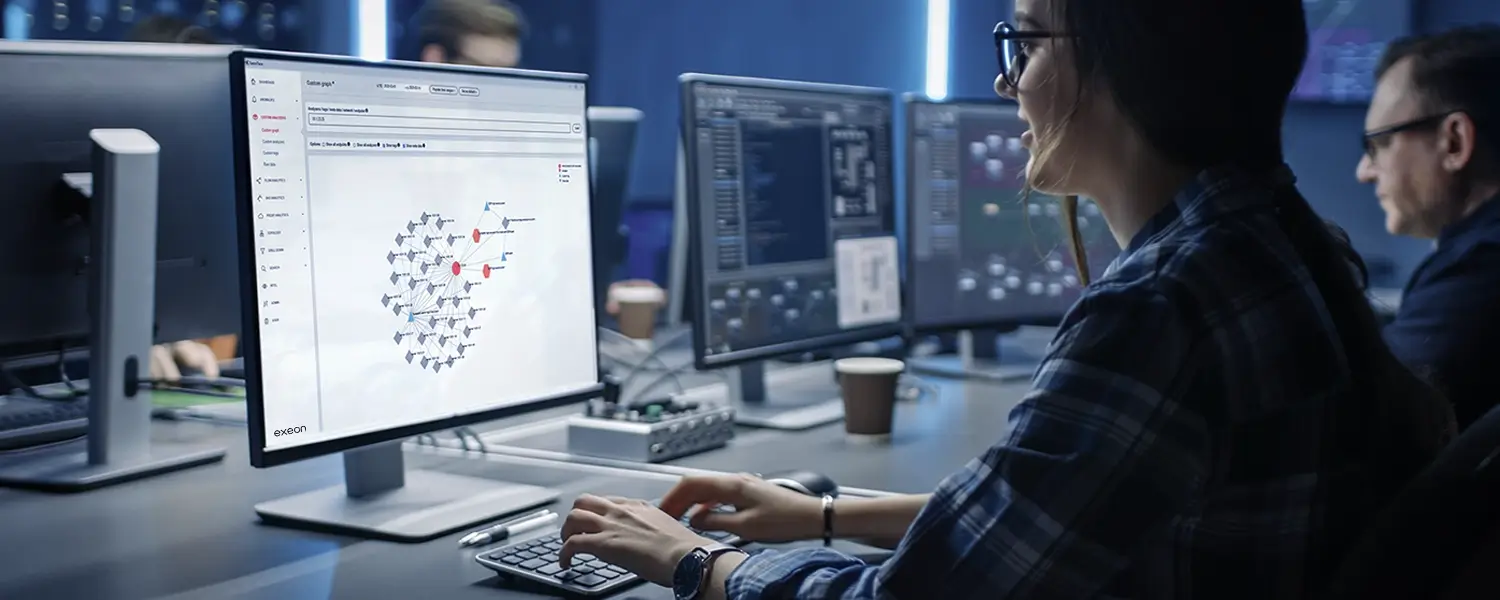
Helping modern SOCs across all security fronts
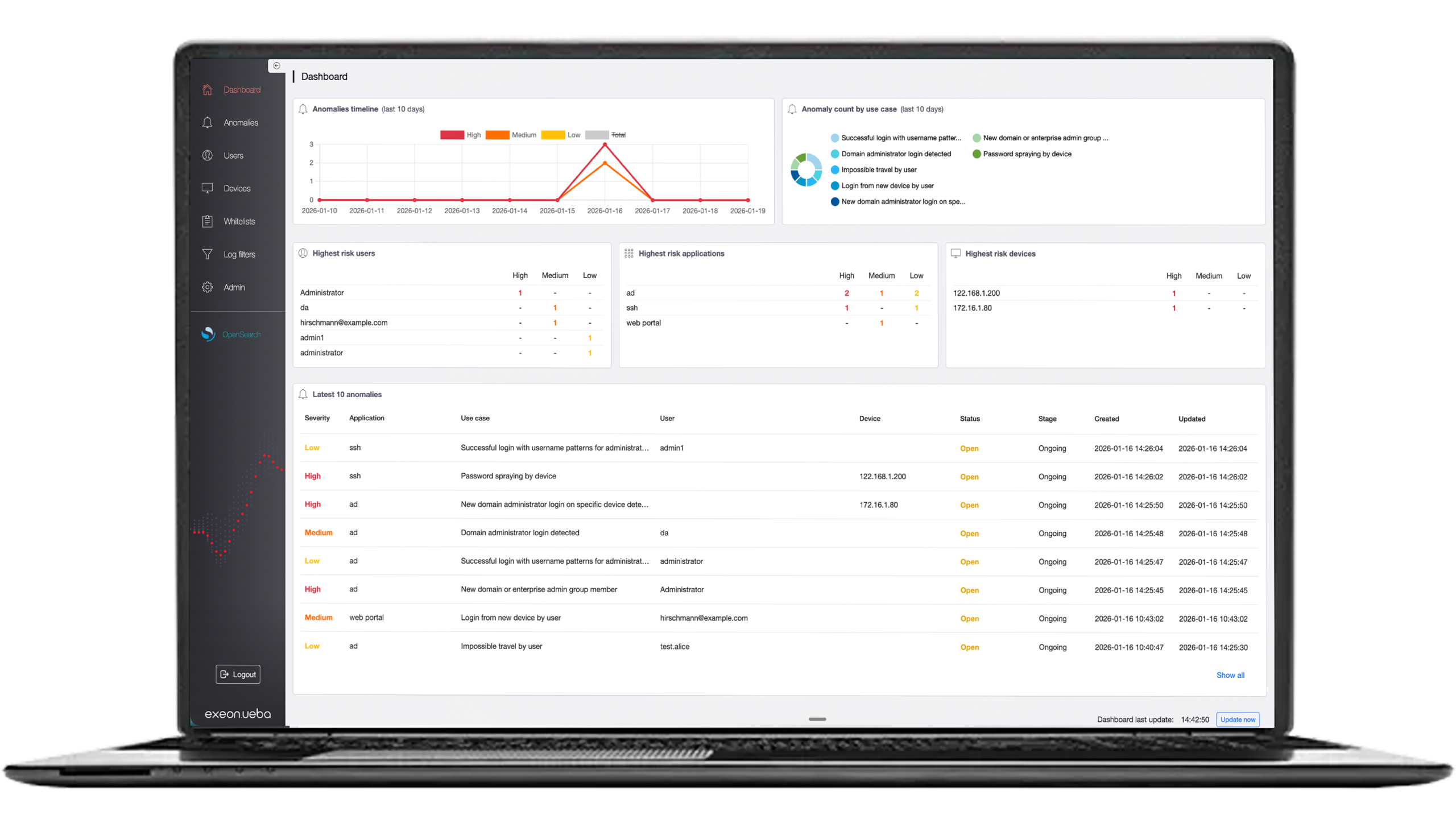
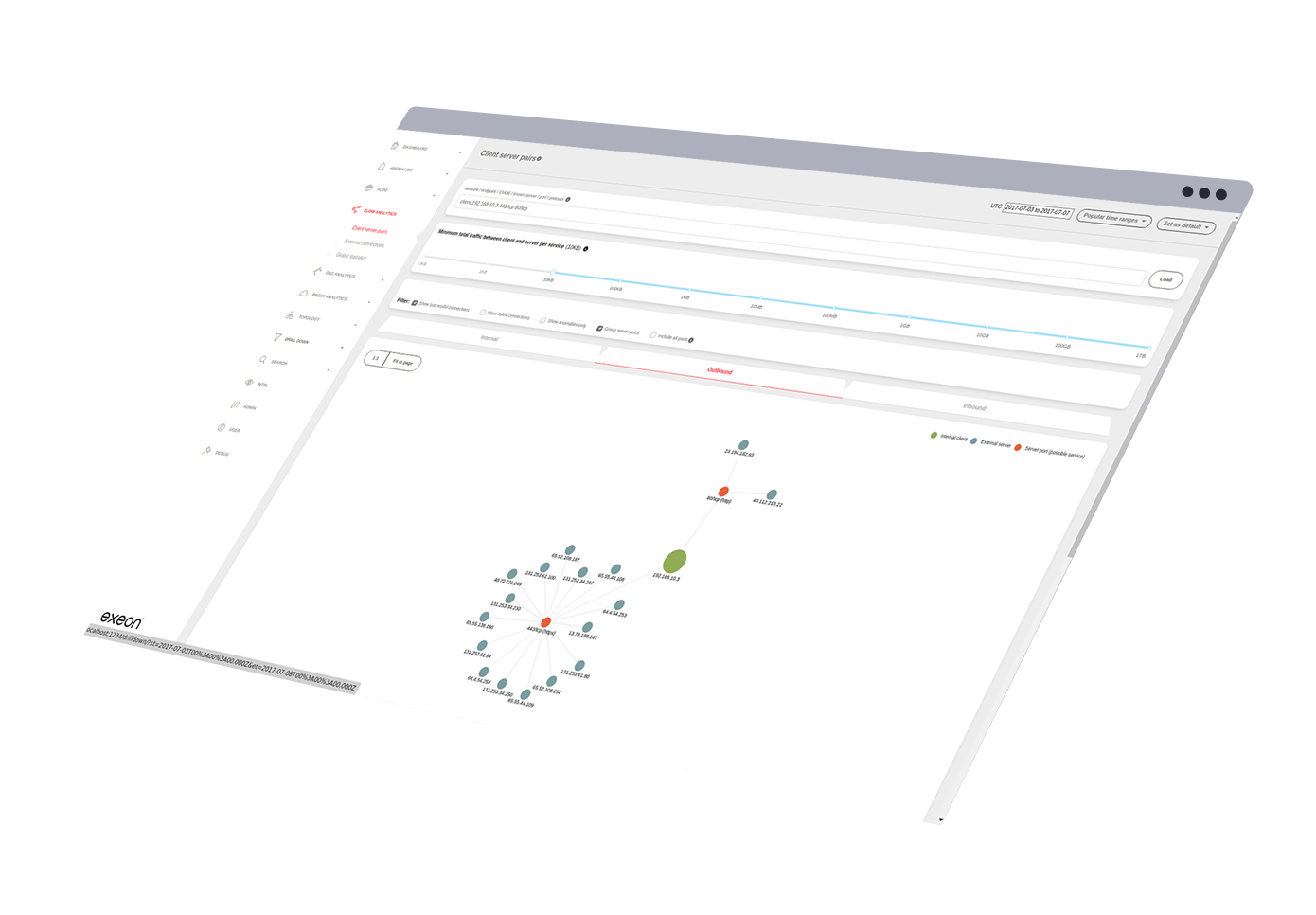
360° visibility
Exeon streams wire data and logs from on-prem, multicloud, IoT and OT segments, closing the blind spots that endpoint tools miss.
- Real-time insights for technical & non-technical stakeholders.
- Unifies IT/OT telemetry in one graph for early lateral-movement detection.
- Enriches SIEM events with AI-driven behavioral context, boosting true-positive rates.
Rapid & easy integrations
Our product integrates via Open REST and syslog APIs into any SIEM, SOAR or EDR stack.
- Being API-based, it allows for an impressive amount of customization to suit the institution's specific needs.
- Optimizes SIEM systems to reduce costs significantly.
- Enhances EDR where EDR agents fall short (e.g., IoT, OT, BYOD).
Built-in compliance and audit readiness
Automated reports map live telemetry to NIS2 Articles 21 & 23, DORA Art. 15 and ISO 27001 A.12.4, while tamper-proof, pseudonymized logs tick GDPR Art. 32 boxes.
- Network monitoring, alerting, and detailed reporting.
- Central storage for GDPR-compliant forensics logs for retrospective analytics.
- Continuously refine detection models for future-proof defense.
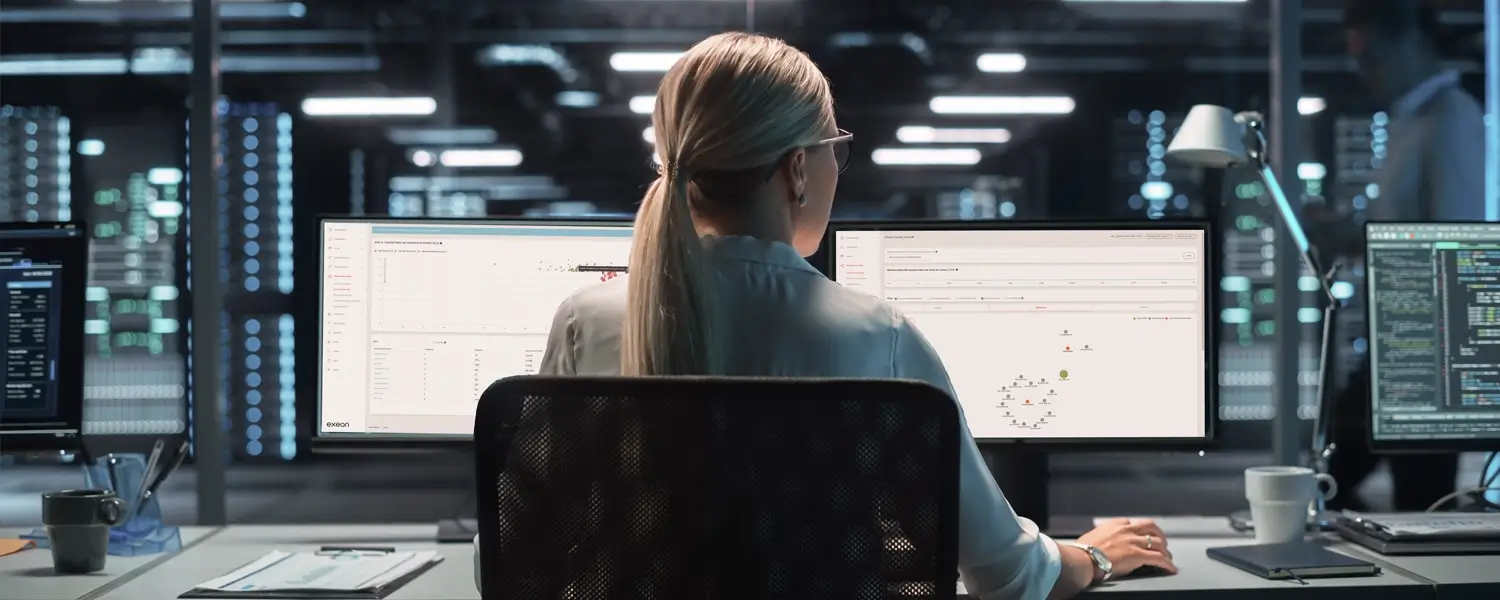
Elevated SOC staff efficiency
Thanks to precise technology that detects advanced
threats ranging from zero-day to APTs and insider
threats, SOC teams experience reduced workloads.
- Dramatically fewer false positives: SOC analysts can concentrate on real threats instead of dealing with alert fatigue.
- Can immediately engage response measures by linking with SOAR playbooks and firewalls.
- Correlates network data and other log sources, identifies anomalies and initiates remedial countermeasures.
AI-powered, automated, and built for modern cyber threats
High SOC efficiency
Exeon’s AI-driven, automated threat detection and response product enhances SOC efficiency and helps manage cyber threats much more effectively.
Real-time monitoring
Easy integrations & deployment
Integrates seamlessly with EDR, NDR, and SIEM systems to provide real-time monitoring across IT, OT, and cloud environments.
Overhead & cost savings
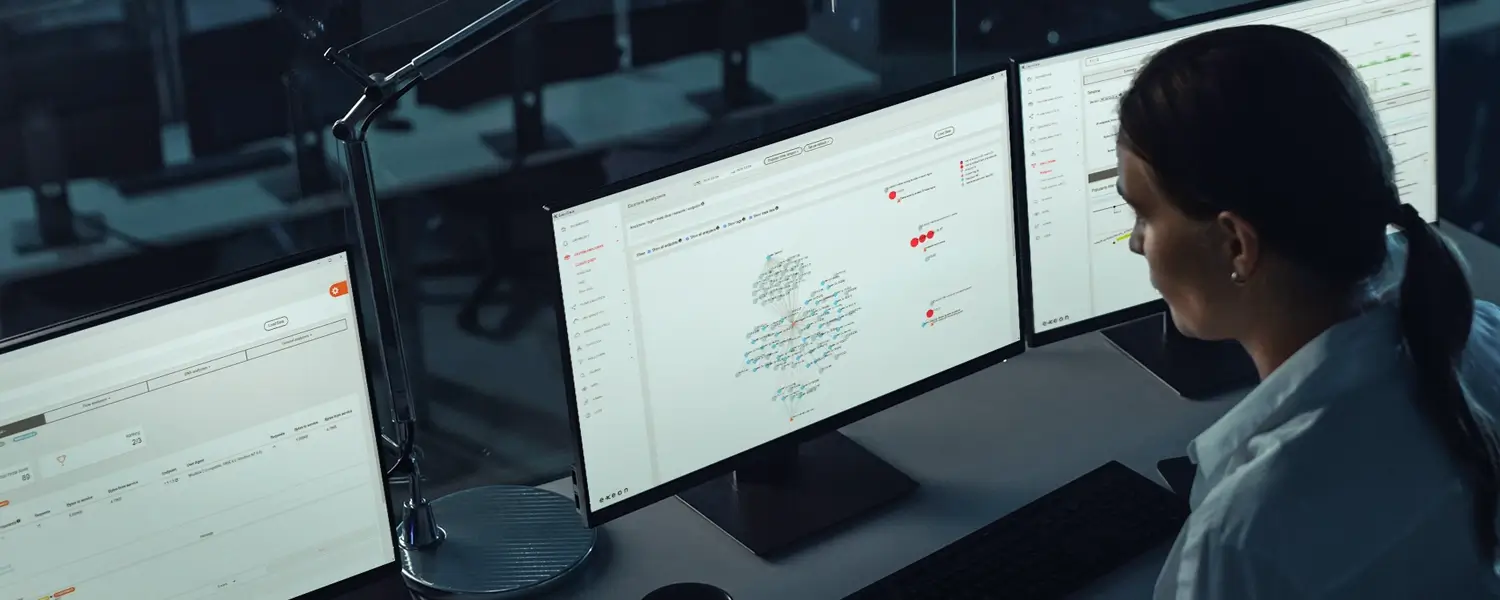
The four steps of SOC+ with Exeon
01Seamless integration
Exeon enhances SOCs by integrating with EDR, NDR, SIEM, and SOAR tools, optimizing threat detection while reducing storage and processing costs.
02Holistic visibility & intelligent detection
AI-powered algorithms establish baseline behaviors, detect anomalies, and uncover threats across networks, cloud, and IoT environments.
03Swift responses
Exeon integrates with SOAR playbooks and firewalls to take immediate action against threats, reducing response times and mitigating potential damage.
04Compliance & long-term resilience
Ensures compliance with NIS2, DORA, and KRITIS, centralizes GDPR-compliant logs, and continuously refines detection models for future-proof defense.
Related solutions for you
Integration
Seamlessly connects with EDR, NDR, and SIEM systems, improving threat detection and optimizing alert processing to reduce storage and processing costs.
Scalability
Exeon products seamlessly scale your SOC, integrating with your hybrid environment to ensure complete visibility across cloud and on-premises infrastructure.
Trusted by global organizations
















Your NIS2 Compliance Checklist
Insights from our security experts
Cut through the cyber noise: blogs written by our thought leaders in AI-powered cybersecurity.