XDR – A new weapon in the fight against cyber threats
Today, companies collect huge amounts of security-relevant data for cyber monitoring. But the problem lies in efficiently analyzing this data - especially across different data sources. Extended Detection and Response (XDR) reveal new possibilities with the help of AI.
Cyber attackers always find loopholes that allow them to circumvent existing protection mechanisms and infect a company with malicious software. To proactively find such loopholes and to quickly detect already infected systems, detection mechanisms are an important part of today's security strategies. Companies use such methods as Network Detection & Response (NDR), Endpoint Detection & Response (EDR) or classic Intrusion Detection Systems (IDS). All these components continuously create and collect data for their area of application. In addition, log data from prevention mechanisms, such as antivirus software or firewalls, as well as from host and application programs are also available.
The challenge is to detect cyber threats quickly and reliably in this haystack of diverse information. Many companies find it difficult to create a holistic threat detection system. Security Incident and Event Management (SIEM) solutions are strong at collecting this data, but cross-data analysis is difficult with this technology because query languages are often complicated, correlation systems scale poorly, and there is a lack of automated threat detection scenarios. As a result, security teams must gather threat-related events from thousands of SIEM events and manually build an overall picture for analysis. This comes at a high price: according to a study by the Enterprise Strategy Group, more than half of critical security alerts are not even perceived as such.
Consolidation of monitoring and cyber defense
A new cybersecurity technology that relies on artificial intelligence (AI) and big data algorithms promises a remedy: "Extended Detection and Response" (XDR). XDR abstracts, correlates and consolidates the information from the various data sources and thus creates an informative overall picture of the threat situation of an IT infrastructure. With machine learning for general anomaly detection and specialized algorithms for detecting typical attack patterns, the infrastructure is monitored holistically. XDR thus enables automated, faster detection of threats, since attacks often occur over several channels and thus appear more clearly in an overall picture. Furthermore, the combined examination of different information sources allows false alarms to be eliminated more quickly and the relevant threats to be prioritized. XDR can also play to its strengths in investigation and defense by providing security teams with more context about the threat, summarizing its extent across sources or systems, and suggesting ways to eliminate it.
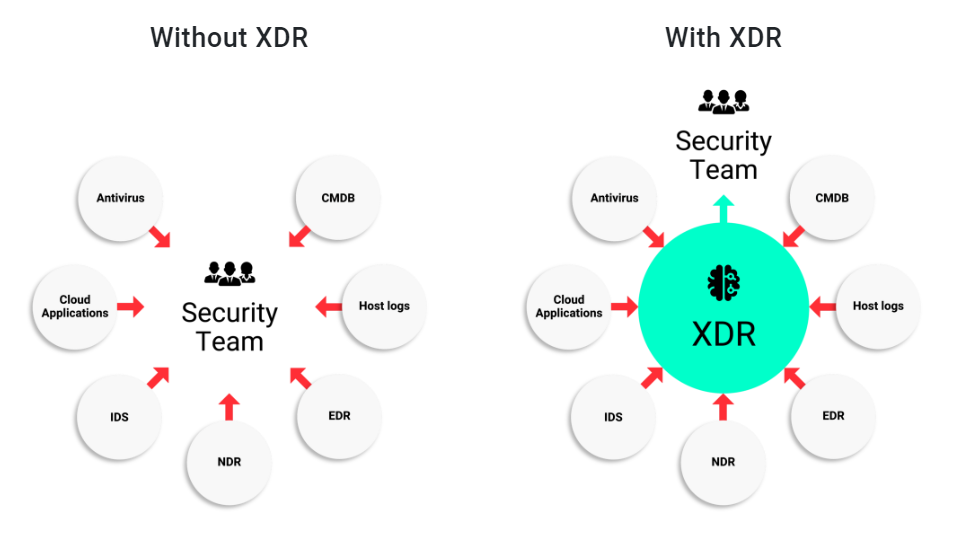
XDR becomes the connection between the individual tool landscape and the security team.
With these features, XDR is one of the current trends in cybersecurity. By consolidating and automatically analyzing existing data from individual systems for anomalies and threat patterns, XDR detects threats that were previously hidden in the background noise of regular IT activities. In addition, XDR enables security teams to efficiently implement detection scenarios and investigate alerts faster because they are delivered directly with aggregated contextual information. In this way, XDR strengthens cyber defense exactly where it so far has had its greatest weaknesses.
Originally published in Netzwoche on November 16th, 2020.

Author:
David Gugelmann
Co-CEO & Founder
email:
david.gugelmann@exeon.com
Share:
Published on:
01.12.2020