CISO Challenge #12
I don’t know whether I can trust the third-party applications in my network
Recent supply chain attacks (Sunburst, Microsoft or Kaseya) have shown how vulnerable third-party providers can be – opening doors into corporate networks
Exeon’s approach
- All network traffic is analysed – including third-party applications
Benefits for CISOs and security teams
- Complete transparency of the entire network
- Early detection of potential malware
- Immediate recognition of network traffic anomalies
Why Global Organizations Love ExeonTrace

Comprehensive Visibility
Visibility into your entire IT/OT network and all its interfaces to identify vulnerabilities (exposed services, shadow IT etc.) and malicious attack patterns in real-time.

Unaffected by Encryption
Algorithms are unaffected by encrypted payloads since they are built to detect attack patterns based on metadata and not deep packet inspection.
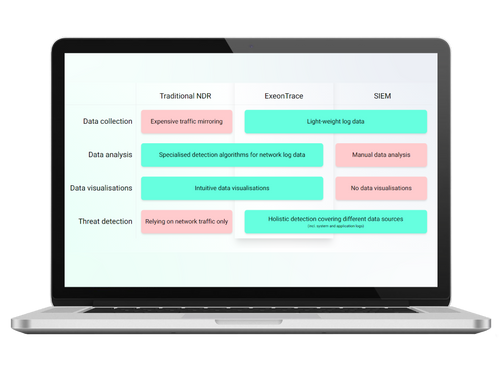
Light-weight Log Data
Analysis of light-weight network log data instead of data-heavy traffic mirroring. Metadata can be exported from existing network sources (switches, firewalls etc.) without hardware sensors.

100% Swiss
As an established Swiss NDR solution, based on a decade of research at ETH Zürich, we maintain a high level of innovation and privacy, which is incorporated in our ExeonTrace platform.