CISO Challenge #7
It is cumbersome for security analysts to analyse the data stored in the SIEM
SIEM queries tend to be highly CPU-intensive as there is lots of unprocessed data that needs to be analysed. In addition, SIEMs typically come with very little, pre-defined network-specific use cases, making SIEM analysis time-consuming for security analysts.
Exeon’s approach
- ExeonTrace’s algorithms process the input data to a graph database that reduces the data size compared to the input data by the factor x100
- This makes data analysis/threat hunting in ExeonTrace extremely performant
- ExeonTrace comes with pre-defined use cases making manual queries obsolete
- Intuitive visualisations support the work of the security analysts
Benefits for CISOs and security teams
- Light-weight graph database analysis accelerates the speed of queries
- Pre-defined use cases reduce the manual work of security analysts
- Out-of-the-box visualisation for threat hunting
- Efficiency gain for SOCs
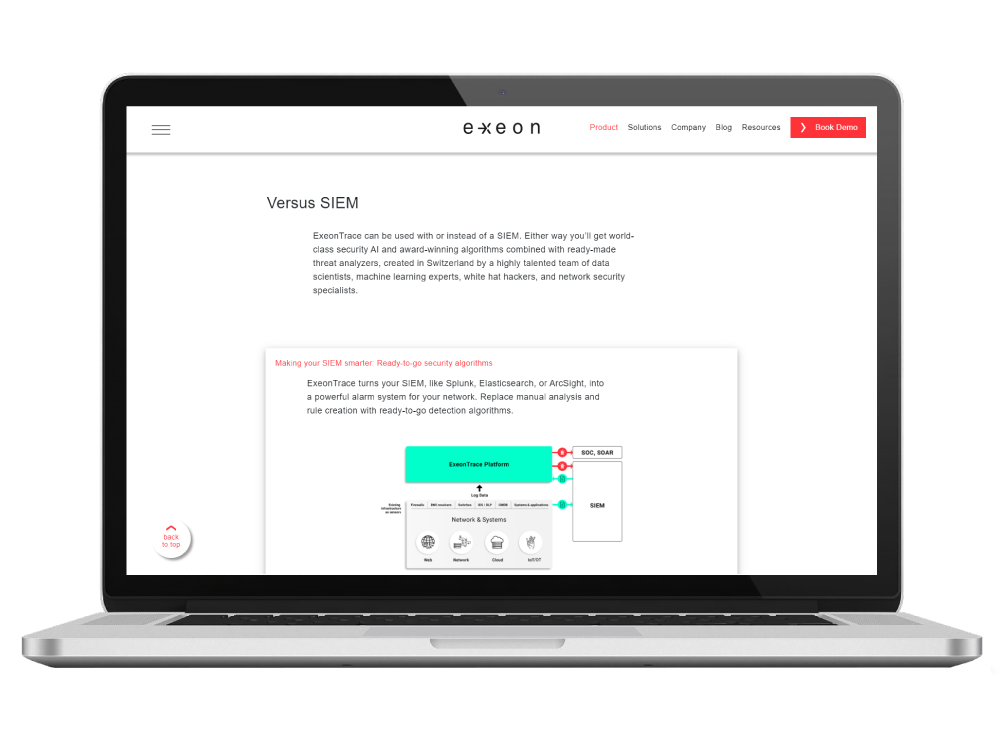
ExeonTrace vs. SIEM
NDR, the smarter way
ExeonTrace can be used with or instead of a SIEM. Either way you’ll get world-class security AI and award-winning algorithms combined with ready-made threat analyzers, created in Switzerland by a highly talented team of data scientists, machine learning experts, white hat hackers, and network security specialists.
Why Global Organizations Love ExeonTrace

Comprehensive Visibility
Visibility into your entire IT/OT network and all its interfaces to identify vulnerabilities (exposed services, shadow IT etc.) and malicious attack patterns in real-time.

Unaffected by Encryption
Algorithms are unaffected by encrypted payloads since they are built to detect attack patterns based on metadata and not deep packet inspection.
Light-weight Log Data
Analysis of light-weight network log data instead of data-heavy traffic mirroring. Metadata can be exported from existing network sources (switches, firewalls etc.) without hardware sensors.

100% Swiss
As an established Swiss NDR solution, based on a decade of research at ETH Zürich, we maintain a high level of innovation and privacy, which is incorporated in our ExeonTrace platform.