Today, most Network Detection and Response solutions rely on traffic mirroring and deep packet inspection (DPI). Traffic mirroring is typically deployed on a single core switch to provide a copy of the network traffic to a sensor that uses DPI to thoroughly analyze the payload. While this approach provides detailed analysis, it requires large amounts of processing power and is blind when it comes to encrypted network traffic.
Metadata analysis has been specifically developed to overcome these limitations. By utilizing metadata for analysis, network communications can be observed at any collection point and be enriched by information providing insights about encrypted communication.
NDR solutions have become crucial to reliably monitor and protect network operations. However, as network traffic becomes encrypted and data volumes continue to increase, most traditional solutions reliant on deep packet inspection are reaching their limits. This begs the question: What detection technologies should organisations utilise to ensure maximum system security?
This article will shed light on the concept of DPI and metadata analysis. We will compare both detection technologies and examine how modern NDR solutions can effectively protect IT/OT networks from advanced cyber threats.
What is Deep Packet Inspection (DPI), and how does it work?
Deep Packet Inspection (DPI) is a comprehensive method of network traffic monitoring that inspects packets flowing across a specific switch or connection point. In most implementations, the entire traffic is mirrored from a core switch to a DPI sensor, which examines both the header and payload of each packet. When the payload is unencrypted, DPI can provide rich, detailed information for robust analysis. Although many traditional NDR solutions still rely on deep packet inspection, the rapid expansion of attack surfaces and evolving IT environments increasingly expose its limitations.
Why is DPI not enough to detect advanced cyberattacks?
Organisations are increasingly using encryption to protect their network traffic and online interactions. Although encryption brings enormous benefits to online privacy and cybersecurity, it also provides a good opportunity for cybercriminals to hide in the dark when launching devastating cyberattacks.
As DPI technology was not built for the analysis of encrypted traffic, it has become blind to the inspection of encrypted packet payloads. This is a significant shortfall for DPI since most modern cyberattacks, such as APT, ransomware, and lateral movement, heavily utilise encryption in their attack routine to receive attacks instructions from remote Command and Control Servers (C&C) scattered across the cyberspace. In addition to absent encryption capabilities, DPI requires large amounts of processing power and time in order to thoroughly inspect the data section of packets.
Consequently, DPI cannot inspect all network packets in data-heavy networks, making it an unfeasible solution for high-bandwidth networks.
The new approach: Metadata analysis
Metadata analysis has been developed to overcome the limitations of DPI. By utilising metadata for network analysis, security teams can monitor all network communications passing through any physical, virtualised or cloud networks without inspecting the entire data section of each packet.

Consequently, metadata analysis is unaffected by encryption and can deal with ever-increasing network traffic. In order to provide security teams with real-time intelligence of all network traffic, metadata analysis captures vast arrays of attributes about network communications, applications, and actors (e.g. user logins). For instance, for every session passing through the network, the source/destination IP address, session length, protocol used (TCP, UDP), and the type of services used are recorded.
Metadata can capture many other key attributes, which effectively help detect and prevent advanced cyberattacks:
- Host and server IP address, port number, geo-location information
- DNS and DHCP information mapping devices to IP addresses
- Web pages accesses along with the URL and header information
- Users to systems mapping using DC log data
- Encrypted web pages – encryption type, cypher and hash, client/server FQDN
- Different objects hashes – such as JavaScript and images
DPI vs. metadata analysis: Which technology suits modern NDR needs?
Choosing the right detection technology is crucial for securing and monitoring modern networks. Deep Packet Inspection (DPI) has long been a core component of traditional NDR solutions, but its limitations are becoming more evident as networks grow in complexity and encryption becomes widespread. Metadata analysis offers a more scalable and efficient alternative, addressing the challenges DPI struggles to overcome.
Below is a detailed comparison of their key differences:
Handling Encryption:
DPI is unable to analyze the payload of encrypted packets, leaving blind spots in network visibility. In contrast, metadata analysis is unaffected by encryption, providing reliable insights into all network traffic, regardless of encryption status.
Resource Intensity:
DPI requires significant processing power and storage, making it resource-intensive and challenging to scale in high-bandwidth networks. Metadata analysis, however, uses lightweight data, making it far more efficient and scalable.
Scalability:
While DPI struggles to handle increasing data volumes and bandwidth, metadata analysis is designed to cope with modern network demands, ensuring seamless performance even as traffic grows.
Data Storage:
Long-term storage of historical data is often impractical or prohibitively expensive with DPI due to the sheer volume of information it collects. Metadata analysis enables cost-effective storage, facilitating forensic investigations and historical analysis.
Real-Time Visibility:
In data-heavy environments, DPI often experiences delays in providing insights. Metadata analysis delivers real-time intelligence, helping security teams respond to threats immediately.
Cost Efficiency:
DPI’s reliance on hardware and intensive processing makes it a costlier solution. Metadata analysis is more budget-friendly, thanks to its lightweight data collection and processing.
By addressing the limitations of DPI, metadata analysis offers a future-proof solution for modern NDR needs, ensuring comprehensive visibility and protection for today’s dynamic IT environments.
How can security teams benefit from metadata?
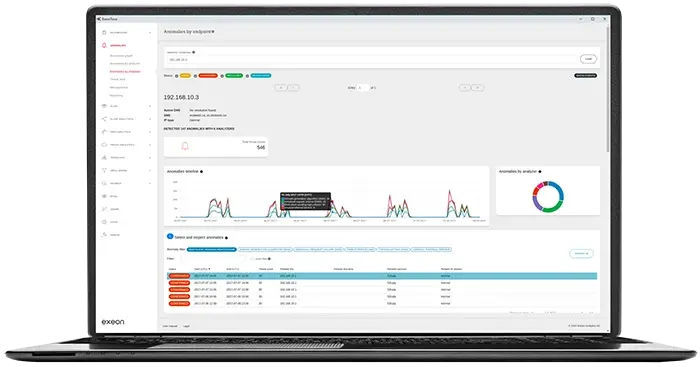
Implementing a Network Detection and Response (NDR) solution based on metadata analysis provides security teams with reliable insights on what happens inside their network – no matter whether the traffic is encrypted or not.
Metadata analysis supplemented by system- and application-logs allow security teams to detect vulnerabilities and improve internal visibility into blind spots, such as shadow IT devices, which are considered a common entry point exploited by cybercriminals.
This holistic visibility is not possible with DPI-based NDR solutions. In addition, light-weight metadata allow for efficient log data storage of historical records, facilitating forensics investigations. Data-heavy DPI analysis makes long-term storage of historical data practically infeasible or very expensive.
Finally, the metadata approach allows security teams to figure out the source of all traffic passing through corporate networks and monitor suspicious activity on all devices connected to networks, such as IoT devices. This makes complete visibility into corporate networks possible.