Look who entered your library!
How the recent discovery of a backdoor in the XZ Utils package, which includes the liblzma library, highlights the ongoing challenges of dealing with supply chain attacks, and how to prevent and detect them.
Backstory of the backdoor
This past March 2024, a developer accidentally discovered the backdoor while investigating mysterious performance issues with SSH connections. Even though the major Linux distributions gave consent for their stable versions, the backdoor was found in various Linux variants, some unstable versions, and in the Homebrew toolkit for macOS.
The backdoor, known as CVE-2024-3094, was introduced through complex obfuscations in the upstream tarballs of xz, starting with version 5.6.0. The security vulnerability has been discovered in the XZ Utils package, which contains tools for handling compressed files in the .xz format. The CVE-2024-3094 backdoor allows unauthorized access to data processed by software that relies on it.
Of particular concern is its impact on OpenSSH servers, which are commonly found in Linux distributions and routinely enabled for system maintenance.
By exploiting this vulnerability, attackers could potentially gain access to SSH servers without requiring proper authentication, posing a significant security risk. It allows an attacker to inject code and remotely execute commands.
The suspected author of this backdoor appears to be a developer, who was actively involved in the XZ Utils package project. Through a regrettably very clever approach, he managed to inject the malicious code into the test versions or rolling release of some Linux distributions.

As of today, researchers are not 100% sure on how the backdoor exactly works (only that it is made very clever) and whether it has already been exploited by attackers, but it shows a potentially high danger for networks and systems.
The threat of supply chain attacks is real
The discovery of this backdoor highlights the constant need for better security practices. It is imperative that companies and organizations constantly check their systems for possible compromises and ensure that all relevant security updates are applied. This case has reignited the debate about embargoes on the disclosure of security vulnerabilities.
While some argue for openness, others defend the usual communication embargoes at Zero-Days and potential exploits. Regardless of that, companies should take the best possible measures to protect their systems and see this latest development as a wake-up call to step up their efforts to keep the systems secure.
A very important takeaway is that this attack was only discovered by chance, and backdoors could already be in all the software that is widespread in enterprise systems. So, along with the constant need to always update their machines right away, companies should be able to detect intruders that exploit backdoors to (already?!) move within their networks.

The best way to foster the security strategy against supply chain attacks and Zero-Day exploits is with an AI-powered Network Detection & Response (NDR) solution for complete visibility of the network’s communication.
Unlocking detection: How NDR detects backdoors, Zero-Day exploits, and supply chain attacks
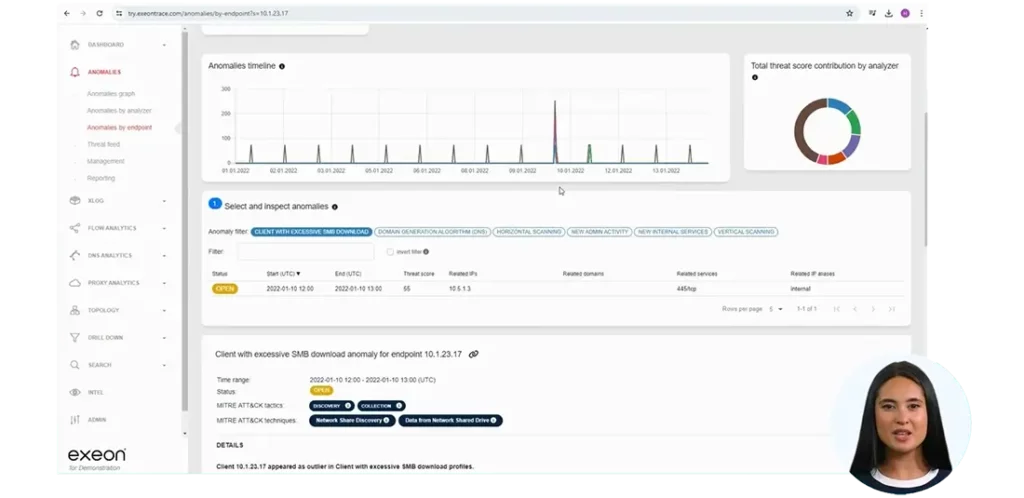
And this is why: an AI-based NDR solution continuously analyzes network metadata and applies behavioral analytics to detect abnormal system behavior. The detection of unusual connections and/or usage of compromised systems for moving within the network allows it to identify unusual patterns that could indicate a backdoor or a Zero-Day exploit.
Unlike traditional security solutions that require agents or sensors to be installed on each device, the agent- and sensorless NDR solutions like Exeon.NDR can monitor OS and workload behaviors across all environments. This approach allows us to detect malicious attack patterns in real time, even in encrypted traffic.
In the context of supply chain attacks, this means they can detect if an attacker is trying to exploit a vulnerability in a third-party component of the network.
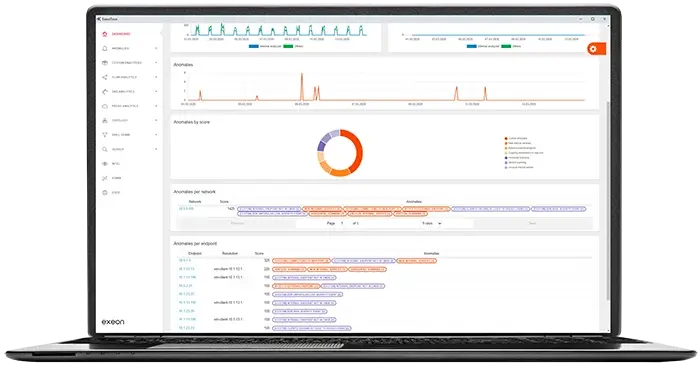
Exeon.NDR employs advanced AI algorithms to analyze network data flows, identifying unusual patterns indicative of malicious activity.
Also, unlike traditional NDR solutions, it operates with lightweight traffic metadata, eliminating the need for costly traffic mirroring and enabling real-time detection of attack patterns. As it offers comprehensive visibility across the entire IT/OT, enabling the identification of vulnerabilities and malicious patterns, and a broad visibility into third-party components, it allows a swift detection of supply chain attacks.
The bottom line
The recent discovery of a backdoor in the XZ Utils package and the liblzma library underscores the persistent threat of supply chain attacks, prompting a critical reassessment of cybersecurity measures. An AI-powered NDR solution like Exeon.NDR offers comprehensive network monitoring and behavioral analytics, enabling real-time detection of backdoors, Zero-Day exploits, and supply chain attacks.
With its ability to analyze network data flows and identify unusual patterns, Exeon.NDR truly provides unparalleled visibility and protection against emerging threats, reinforcing the importance of robust security strategies in safeguarding against potential breaches.
But how does it work for my organization exactly?
Request one of our free demo videos or ask for your live tour to see how Exeon.NDR works for your organization and systems below.
How can Exeon protect your network and detect supply chain attacks?
Watch our recorded demo of a cyber attack to see exactly how Exeon.NDR works.


